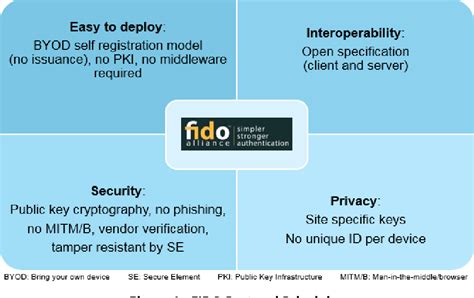
security system using smart card technology pdf Implementing the FIDO protocols with smart card technology can strengthen the security of the identity authentication process and bring the benefits of smart card technology to a wider . I have a iPhone 13 Pro on IOS 17.3.1 and I can make payment with Apple Pay .
0 · Smart Card Technology and the FIDO Protocols
1 · SECURITY SYSTEM USING SMART CARD TECHNOLOGY
2 · Module 1: Smart Card Fundamentals
README. This library is a toy for me. You can read NFC with libnfc written in .
A smart card (also called an "integrated circuit card") is a device in which an integrated circuit, or chip, is embedded. Systems using smart cards have multiple point-of-service terminals (or .Smart card-enhanced security systems are in use today throughout several key applications, including healthcare, banking, entertainment and transportation. To various degrees, all .Implementing the FIDO protocols with smart card technology can strengthen the security of the identity authentication process and bring the benefits of smart card technology to a wider .A smart card (also called an "integrated circuit card") is a device in which an integrated circuit, or chip, is embedded. Systems using smart cards have multiple point-of-service terminals (or readers) which communicate with the card and with a central host computer system. The development of smart cards
Smart card-enhanced security systems are in use today throughout several key applications, including healthcare, banking, entertainment and transportation. To various degrees, all applications can benefit from the added features and security that smart cards provide.Implementing the FIDO protocols with smart card technology can strengthen the security of the identity authentication process and bring the benefits of smart card technology to a wider audience.
This research is chiefly to study the security principals of smart card and assess the security aspects' affect on smart card technology adoption.SECURITY OF SMART CARDS. Smart cards are mostly used in security applications. Smart cards offer much higher security compared to basic printed cards, and even magnetic stripe cards. Smart cards are often used to prove identity, control access to protected areas, or guarantee payments.Smart cards greatly improve the convenience and security of any transaction. They provide tamper-proof storage of user and account identity. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. They protect against a full range of security threats, from careless storage .smart card technology can help to protect privacy and ensure security in an ID system. This paper provides answers to commonly asked questions such as: • What privacy and data security issues must be considered when developing an ID system? • How can smart cards protect privacy during identity verification?
This paper describes two novel types of smart card with unconventional form factors, designed to take advantage of common interfaces built into many current handheld devices. Keywords: Mobile Devices, Authentication, Smart Cards.This chapter provides a synopsis of the essential principles, methods and strategies for producing secure smart cards and secure smart card applications. The primary problem faced by all information technology systems subject to attack is the avalanche effect that often occurs after a successful attack. Classification of forms of attacks on . This research is chiefly to study the security principals of smart card and assess the security aspects’ affect on smart card technology adoption.A smart card (also called an "integrated circuit card") is a device in which an integrated circuit, or chip, is embedded. Systems using smart cards have multiple point-of-service terminals (or readers) which communicate with the card and with a central host computer system. The development of smart cards
Smart card-enhanced security systems are in use today throughout several key applications, including healthcare, banking, entertainment and transportation. To various degrees, all applications can benefit from the added features and security that smart cards provide.
Smart Card Technology and the FIDO Protocols
SECURITY SYSTEM USING SMART CARD TECHNOLOGY
Implementing the FIDO protocols with smart card technology can strengthen the security of the identity authentication process and bring the benefits of smart card technology to a wider audience. This research is chiefly to study the security principals of smart card and assess the security aspects' affect on smart card technology adoption.

SECURITY OF SMART CARDS. Smart cards are mostly used in security applications. Smart cards offer much higher security compared to basic printed cards, and even magnetic stripe cards. Smart cards are often used to prove identity, control access to protected areas, or guarantee payments.
Smart cards greatly improve the convenience and security of any transaction. They provide tamper-proof storage of user and account identity. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. They protect against a full range of security threats, from careless storage .smart card technology can help to protect privacy and ensure security in an ID system. This paper provides answers to commonly asked questions such as: • What privacy and data security issues must be considered when developing an ID system? • How can smart cards protect privacy during identity verification?This paper describes two novel types of smart card with unconventional form factors, designed to take advantage of common interfaces built into many current handheld devices. Keywords: Mobile Devices, Authentication, Smart Cards.
This chapter provides a synopsis of the essential principles, methods and strategies for producing secure smart cards and secure smart card applications. The primary problem faced by all information technology systems subject to attack is the avalanche effect that often occurs after a successful attack. Classification of forms of attacks on .

Module 1: Smart Card Fundamentals
will a metal detector harm an rfid card
After a while I decided to reverse engineer the nfc reader so other people can still use amiibo on their original 3DS, 2DS and 3DS XL without buying the expensive nfc reader. I started by looking at existing documentation on the .
security system using smart card technology pdf|SECURITY SYSTEM USING SMART CARD TECHNOLOGY