hacking a smart phone through a micro sd card 7 ways to hack a phone. Social engineering; Malvertising; Smishing; Malware; Pretexting; Breaking in via Bluetooth; Man-in-the-middle Wi-Fi attacks; 1. Social engineering
1. Open your phone’s app store: Go to the app store on your smartphone. If you have an Android device, open the Google Play Store, and if you have an iPhone, open the App Store. 2. Search for an NFC reader app: In .NFC enabled phones can ONLY read NFC and passive high frequency RFID (HF-RFID). These must be read at an extremely close range, .
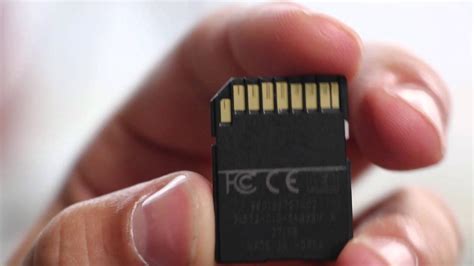
0 · sd card memory hacking
1 · sd card hacking camera
2 · sd card hacking
3 · micro sd card hacking
4 · memory card hacking software
5 · memory card hacking
Saturday, January 10, 2015AFC: New England Patriots 35, Baltimore Ravens 31With only 13 rushing attempts for 14 total yards, New England . See more
rfid chip companies supply chain
sd card memory hacking
These forms of modified microSD cards can reportedly allow hackers to take over your smartphone by using the memory in the SD card to infect Android devices. Thankfully, most smartphones now have sufficient memory and users have slowed down in their demand for . One of them addressed hacking the memory controllers embedded in all memory cards that you may have. As memory storage density increases, it’s more likely that some . These forms of modified microSD cards can reportedly allow hackers to take over your smartphone by using the memory in the SD card to infect Android devices. Thankfully, most smartphones now have sufficient memory and users have slowed down in their demand for microSD cards.
sd card hacking camera
One of them addressed hacking the memory controllers embedded in all memory cards that you may have. As memory storage density increases, it’s more likely that some sectors inside the embedded.
While SD cards are admittedly I/O-limited, some clever hacking of the microcontroller in an SD card could make for a very economical and compact data logging solution for I2C or SPI-based sensors. Slides from our talk at 30C3 can be downloaded here , or you can watch the talk on Youtube below. 7 ways to hack a phone. Social engineering; Malvertising; Smishing; Malware; Pretexting; Breaking in via Bluetooth; Man-in-the-middle Wi-Fi attacks; 1. Social engineering
One solution is to throw money at the problem and buy a USB breakout board. For the price of a Raspberry Pi and SD card, you can buy an IOIO dev kit that seems to support nearly everything you’d.With USSD codes, also known as quick codes or feature codes, you can quickly check if your phone has been hacked. There are many combinations to diagnose different issues, and with code to check if your phone is monitored, and I'll discuss .
You can hack those small memory chips to perform man-in-the-middle attacks, as shown off by two researchers, Bunnie and xobs, at 30C3 (Computer Chaos Congress). Security researchers have found a way to hack SD Cards, the most common form of flash-memory cards used to store data mobile phones and digital cameras, and run software that intercepts data.This learning track is dedicated to learning the most popular mobile vulnerabilities in both Android and iOS applications. The Android hacking content was created by Daeken and recorded by NahamSec and the iOS module was done by Dawn Isabel, . Andrew “bunnie” Huang and Sean “xobs” Cross have discovered a way to hack even the small microSD cards that go inside current smartphones and tablets to increase their storage, as well as.
These forms of modified microSD cards can reportedly allow hackers to take over your smartphone by using the memory in the SD card to infect Android devices. Thankfully, most smartphones now have sufficient memory and users have slowed down in their demand for microSD cards. One of them addressed hacking the memory controllers embedded in all memory cards that you may have. As memory storage density increases, it’s more likely that some sectors inside the embedded. While SD cards are admittedly I/O-limited, some clever hacking of the microcontroller in an SD card could make for a very economical and compact data logging solution for I2C or SPI-based sensors. Slides from our talk at 30C3 can be downloaded here , or you can watch the talk on Youtube below. 7 ways to hack a phone. Social engineering; Malvertising; Smishing; Malware; Pretexting; Breaking in via Bluetooth; Man-in-the-middle Wi-Fi attacks; 1. Social engineering
One solution is to throw money at the problem and buy a USB breakout board. For the price of a Raspberry Pi and SD card, you can buy an IOIO dev kit that seems to support nearly everything you’d.With USSD codes, also known as quick codes or feature codes, you can quickly check if your phone has been hacked. There are many combinations to diagnose different issues, and with code to check if your phone is monitored, and I'll discuss . You can hack those small memory chips to perform man-in-the-middle attacks, as shown off by two researchers, Bunnie and xobs, at 30C3 (Computer Chaos Congress). Security researchers have found a way to hack SD Cards, the most common form of flash-memory cards used to store data mobile phones and digital cameras, and run software that intercepts data.
This learning track is dedicated to learning the most popular mobile vulnerabilities in both Android and iOS applications. The Android hacking content was created by Daeken and recorded by NahamSec and the iOS module was done by Dawn Isabel, .
sd card hacking
micro sd card hacking
rfid chip dangerous things
rfid chip auf handy kopieren
30pcs NFC Tags Ntag215 Cards NFC Cards Transparent Card Rewritable 504 .
hacking a smart phone through a micro sd card|sd card hacking