ms encrypted smart cards Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual smart cards are less expensive to implement and more convenient for users. Proceed as follows: First open the Settings app on your iPhone. Then select the option “Control Center”. Scroll down and tap the green plus button to the left of “NFC Tag Reader”. The iPhone XS (Max), iPhone XR, iPhone 11 as well as .Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put your iPhone near the NFC tag. Enter a name for your tag. .
0 · Virtual Smart Card Overview
1 · Get Started with Virtual Smart Cards
Here are some common reasons why you might not be able to read NFC tags: Incompatibility with Device: Not all devices are NFC-enabled or support all types of NFC tags. .
Virtual Smart Card Overview
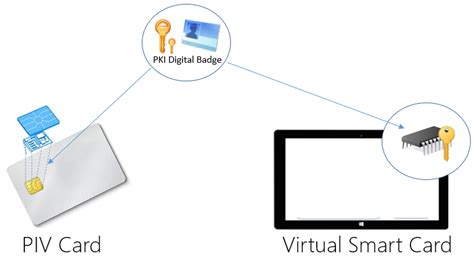
Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of .
By utilizing Trusted Platform Module (TPM) devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three . Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual smart cards are less expensive to implement and more convenient for users. Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) chip that is available on devices.
developer software smart credit card
Get Started with Virtual Smart Cards
By utilizing Trusted Platform Module (TPM) devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three key properties that are desired by smart cards: nonexportability, isolated cryptography, and .
You can use smart card certificates with BitLocker Drive Encryption to protect fixed and removable data drives and to recover BitLocker-protected drives in the absence of the primary access key. Once you have obtained certificates, you can use them with BitLocker data recovery agents and as a BitLocker key protector for data drives. Virtual smart cards (VSC) are a Microsoft solution that provide many of the same benefits with lower costs to organizations. After provisioning virtual smart cards, users only have to enter a PIN to sign in. So, you might ask yourself how this can be two-factor authentication if users only provide this password equivalent as the "know" factor.Install Instructions. Back To Top. Provides an overview of TPM virtual smart cards as an option for strong authentication. Employees and contractors use physical smart card readers to authenticate themselves for secure access to desktops and laptops. Smart cards provide seamless and secure authentication to apps, websites, Wi-Fi, and VPN as well .
The very basics. Public and private keys. Public key cryptography uses some very sophisticated mathematics to embed a secret inside a ‘private key’ from which a corresponding ‘public key’ is then generated. While related, it is generally “extremely difficult” to recreate the private key from the public key.
In TPM virtual smart cards, security is ensured with a secure key hierarchy, which includes several chains of encryption. The chain originates with the TPM storage root key, which is generated and stored within the TPM and never exposed outside the chip. Windows Security Smart Card popup. When starting my computer I get the popup attached below, it comes up and has to be dismissed a total of four times. This happens on two different Windows 10 devices I use. I use a smart card to access enterprise webmail on occasion and that works without issue. Virtual smart cards that utilize a TPM provide the three main security principles of traditional smart cards: nonexportability, isolated cryptography, and anti-hammering. Virtual smart cards are less expensive to implement and more convenient for users.
Virtual smart card technology offers comparable security benefits to physical smart cards by using two-factor authentication. Virtual smart cards emulate the functionality of physical smart cards, but they use the Trusted Platform Module (TPM) chip that is available on devices. By utilizing Trusted Platform Module (TPM) devices that provide the same cryptographic capabilities as physical smart cards, virtual smart cards accomplish the three key properties that are desired by smart cards: nonexportability, isolated cryptography, and . You can use smart card certificates with BitLocker Drive Encryption to protect fixed and removable data drives and to recover BitLocker-protected drives in the absence of the primary access key. Once you have obtained certificates, you can use them with BitLocker data recovery agents and as a BitLocker key protector for data drives.
differences between a credit charge debit and smart card
Virtual smart cards (VSC) are a Microsoft solution that provide many of the same benefits with lower costs to organizations. After provisioning virtual smart cards, users only have to enter a PIN to sign in. So, you might ask yourself how this can be two-factor authentication if users only provide this password equivalent as the "know" factor.
Install Instructions. Back To Top. Provides an overview of TPM virtual smart cards as an option for strong authentication.
Employees and contractors use physical smart card readers to authenticate themselves for secure access to desktops and laptops. Smart cards provide seamless and secure authentication to apps, websites, Wi-Fi, and VPN as well .
The very basics. Public and private keys. Public key cryptography uses some very sophisticated mathematics to embed a secret inside a ‘private key’ from which a corresponding ‘public key’ is then generated. While related, it is generally “extremely difficult” to recreate the private key from the public key. In TPM virtual smart cards, security is ensured with a secure key hierarchy, which includes several chains of encryption. The chain originates with the TPM storage root key, which is generated and stored within the TPM and never exposed outside the chip.

Viewing and listening information for Auburn's home football game vs. LSU is featured. . The Auburn radio coverage can be heard on Sirius/XM Channel 190 as well as the .
ms encrypted smart cards|Virtual Smart Card Overview