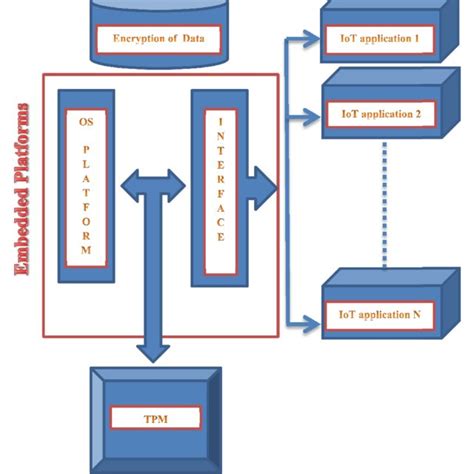
trusted platform module tpm 1.2 security chip smart card reader This article provides a description of the Trusted Platform Module (TPM 1.2 and TPM 2.0) components, and explains how they're used to mitigate dictionary attacks. A TPM is a microchip designed to provide basic security-related functions, primarily involving encryption keys.
The NFC Key Card can be used to unlock and start your car if your phone is not available. You can keep the NFC Key Card in your wallet or purse as a backup. How to Use: Digital Key 2 .
0 · windows security trusted platform module
1 · trusted platform module key
2 · trusted platform module functions
3 · trusted platform module download
4 · trusted platform module certificate
5 · tpm platform module
6 · tpm key storage provider
7 · tpm certificate storage
Card emulation with a secure element. When NFC card emulation is provided using a secure element, the card to be emulated is provisioned into the secure element on the device through an Android application. Then, when .
Users insert a smart card into a built-in or USB card reader and enter a PIN to unlock it. Windows can then access the card's certificate and use the private key for .

Microsoft’s Windows 11 operating system requires a heretofore little-known PC security feature, the Trusted Platform Module (TPM). It could . A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. The chip includes multiple physical security mechanisms to make it tamper .Because of this, TPM 2.0 supports four authorizations which would be analogous to the single TPM 1.2 "owner." In TPM 2.0, the new Platform Hierarchy is intended to be used by platform .The TPM, a secure cryptographic integrated circuit (IC), provides a hardware-based approach to manage user authentication, network access, data protection and more that takes security to .
This article provides a description of the Trusted Platform Module (TPM 1.2 and TPM 2.0) components, and explains how they're used to mitigate dictionary attacks. A TPM is a microchip designed to provide basic security-related functions, primarily involving encryption keys. Users insert a smart card into a built-in or USB card reader and enter a PIN to unlock it. Windows can then access the card's certificate and use the private key for authentication or to unlock BitLocker protected data volumes.
Microsoft’s Windows 11 operating system requires a heretofore little-known PC security feature, the Trusted Platform Module (TPM). It could be cause for concern if you're looking to build. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. The chip includes multiple physical security mechanisms to make it tamper-resistant, and malicious software is unable to tamper with the security functions of the TPM.
Because of this, TPM 2.0 supports four authorizations which would be analogous to the single TPM 1.2 "owner." In TPM 2.0, the new Platform Hierarchy is intended to be used by platform manufacturers. The Storage and Endorsement hierarchies, and the Null hierarchy will be used by operating system's and OS-present applications.
The TPM, a secure cryptographic integrated circuit (IC), provides a hardware-based approach to manage user authentication, network access, data protection and more that takes security to higher level than software-based security. This paper explains how to use and enable the TPM in 4 .A TPM, or Trusted Platform Module, improves the security of your PC by securely creating and storing cryptographic keys. TPM 2.0 is a key part of making Windows 11 even more secure. The Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations.
“The Trusted Platform Modules (TPM) is a chip that is either integrated into your PC’s motherboard or added separately into the CPU,” explains David Weston, director of enterprise and OS.Many devices that run Windows 10 have Trusted Platform Module (TPM) chipsets. There's a security vulnerability in certain TPM chipsets that can affect operating system security, which means Windows 10 operating systems are at an increased risk. This article provides a description of the Trusted Platform Module (TPM 1.2 and TPM 2.0) components, and explains how they're used to mitigate dictionary attacks. A TPM is a microchip designed to provide basic security-related functions, primarily involving encryption keys. Users insert a smart card into a built-in or USB card reader and enter a PIN to unlock it. Windows can then access the card's certificate and use the private key for authentication or to unlock BitLocker protected data volumes.
Microsoft’s Windows 11 operating system requires a heretofore little-known PC security feature, the Trusted Platform Module (TPM). It could be cause for concern if you're looking to build. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. The chip includes multiple physical security mechanisms to make it tamper-resistant, and malicious software is unable to tamper with the security functions of the TPM.Because of this, TPM 2.0 supports four authorizations which would be analogous to the single TPM 1.2 "owner." In TPM 2.0, the new Platform Hierarchy is intended to be used by platform manufacturers. The Storage and Endorsement hierarchies, and the Null hierarchy will be used by operating system's and OS-present applications.The TPM, a secure cryptographic integrated circuit (IC), provides a hardware-based approach to manage user authentication, network access, data protection and more that takes security to higher level than software-based security. This paper explains how to use and enable the TPM in 4 .
A TPM, or Trusted Platform Module, improves the security of your PC by securely creating and storing cryptographic keys. TPM 2.0 is a key part of making Windows 11 even more secure. The Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations.
“The Trusted Platform Modules (TPM) is a chip that is either integrated into your PC’s motherboard or added separately into the CPU,” explains David Weston, director of enterprise and OS.

windows security trusted platform module

network level authentication smart card
$126.00
trusted platform module tpm 1.2 security chip smart card reader|trusted platform module functions