kerberos smart card authentication In this article, we will learn what Kerberos is, how it works, and the various pros and cons of using this authentication protocol. Step 1: Show your credit card near the NFC terminal when the device signals you to. Step 2: The NFC terminal will read your credit card information and process the payments. .
0 · what is kerberos pre authentication
1 · what is kerberos based authentication
2 · kerberos authentication troubleshooting guidance
3 · kerberos authentication step by
4 · kerberos authentication how it works
5 · kerberos authentication guide
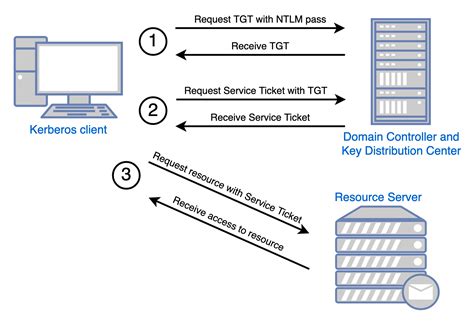
6 · kerberos authentication diagram
7 · explain the authentication standards kerberos with suitable diagram
Nfc-frog supports multiple modes for reading card data. See more
Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to .These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details .When the user uses a smart card to authenticate to a Kerberos realm, he inserts the smart card into the smart card reader connected to his computer. The computer prompts the user for a . In this article, we will learn what Kerberos is, how it works, and the various pros and cons of using this authentication protocol.
Kerberos, on the other hand, also accepts KERB_SMART_CARD_LOGON and KERB_CERTIFICATE_LOGON formats. And that's where the authentication via a physical device, such as a smart . Authentication is a process for verifying the identity of an object or person. When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is .
Kerberos is an authentication protocol significantly safer than normal password-based authentication. With Kerberos, passwords are never sent over the network, even when .Smart cards can be used with Kerberos, but it requires additional configuration to recognize the X.509 (SSL) user certificates on the smart cards: Install the required PKI/OpenSSL package, .

Kerberos sends a request to the Kerberos Distribution Center (KDC) on the domain controller for authentication. The request includes a copy of the x.509 certificate (from the . If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to authentication that is based on user name and password.
These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on configurations and using generic smart cards.When the user uses a smart card to authenticate to a Kerberos realm, he inserts the smart card into the smart card reader connected to his computer. The computer prompts the user for a PIN, which is then sent to the smart card. In this article, we will learn what Kerberos is, how it works, and the various pros and cons of using this authentication protocol.
Kerberos, on the other hand, also accepts KERB_SMART_CARD_LOGON and KERB_CERTIFICATE_LOGON formats. And that's where the authentication via a physical device, such as a smart card, or an external web server comes into play. Authentication is a process for verifying the identity of an object or person. When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an imposter.
Kerberos is an authentication protocol significantly safer than normal password-based authentication. With Kerberos, passwords are never sent over the network, even when services are accessed on other machines.
Smart cards can be used with Kerberos, but it requires additional configuration to recognize the X.509 (SSL) user certificates on the smart cards: Install the required PKI/OpenSSL package, along with the other client packages: [root@server ~]# yum install krb5-pkinit. Kerberos sends a request to the Kerberos Distribution Center (KDC) on the domain controller for authentication. The request includes a copy of the x.509 certificate (from the smart card). If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates. Virtual smart cards were introduced to alleviate the need for a physical smart card, the smart card reader, and the associated administration of that hardware.
what is kerberos pre authentication
Remote Desktop Services enables users to sign in with a smart card by entering a PIN on the RDC client computer and sending it to the RD Session Host server in a manner similar to authentication that is based on user name and password.
These Windows Domain configuration guides will help you configure your Windows network domain for smart card logon using PIV credentials. There are many useful pages and technical articles available online that include details on configurations and using generic smart cards.When the user uses a smart card to authenticate to a Kerberos realm, he inserts the smart card into the smart card reader connected to his computer. The computer prompts the user for a PIN, which is then sent to the smart card. In this article, we will learn what Kerberos is, how it works, and the various pros and cons of using this authentication protocol.
Kerberos, on the other hand, also accepts KERB_SMART_CARD_LOGON and KERB_CERTIFICATE_LOGON formats. And that's where the authentication via a physical device, such as a smart card, or an external web server comes into play.
Authentication is a process for verifying the identity of an object or person. When you authenticate an object, such as a smart card, the goal is to verify that the object is genuine. When you authenticate a person, the goal is to verify that you aren't dealing with an imposter.Kerberos is an authentication protocol significantly safer than normal password-based authentication. With Kerberos, passwords are never sent over the network, even when services are accessed on other machines.Smart cards can be used with Kerberos, but it requires additional configuration to recognize the X.509 (SSL) user certificates on the smart cards: Install the required PKI/OpenSSL package, along with the other client packages: [root@server ~]# yum install krb5-pkinit.
what is kerberos based authentication

1977 Topps Football Walter Payton All-Pro Rookie Card. a. Sold Price: $31,200.00 b. CL Value: $18,748.82 c. Where It Sold: REA. Description: The 1977 Topps Football Walter Payton All-Pro Rookie Card celebrates .
kerberos smart card authentication|kerberos authentication diagram