rfid hacking card steal By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach . Bring music & entertainment wherever you go with SiriusXM. Listen to music, live sports play-by-play, talk & entertainment radio & favorite podcasts.
0 · rfid scanner hack
1 · rfid hacking speed
2 · rfid hacking
3 · rfid card hacked
4 · how to steal rfid cards
5 · how to keep rfid from hacking
6 · can rfid wallet be hacked
7 · can a rfid be hacked
Statewide coverage is the hallmark of the Auburn Sports Network's exclusive coverage of Auburn football. All home and away games are broadcast across the entire state of Alabama plus portions of .
By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach . These often-overlooked security checkpoints have multiple weaknesses that .
Practical guide to RFID hacking for penetration testers. Investigates the latest .
auburn basketball radio broadcast
With the recent shift to contactless payment cards, more cybercriminals are turning to RFID credit card theft via scanning. This article will explain how this theft happens and provide tips on how to protect your RFID credit card from . By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. These often-overlooked security checkpoints have multiple weaknesses that adversaries could exploit to gain illegitimate access to your physical environment. This post covers the technical details of two common attack methods for RFID credential theft.
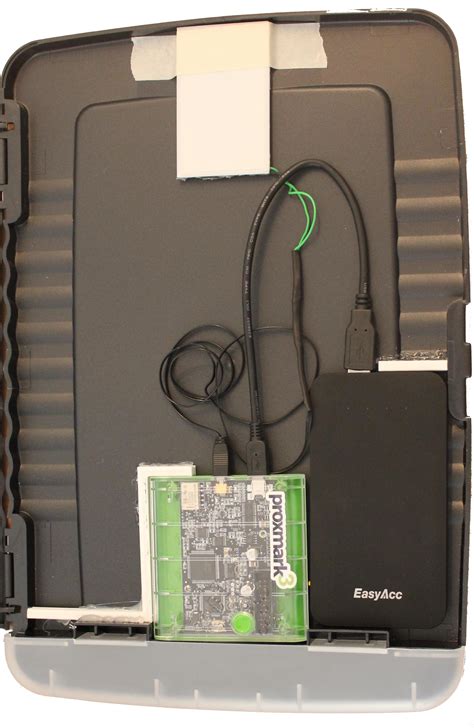
Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.
rfid scanner hack
With the recent shift to contactless payment cards, more cybercriminals are turning to RFID credit card theft via scanning. This article will explain how this theft happens and provide tips on how to protect your RFID credit card from potential thefts and other common payment card frauds. RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently steal this ID info from any RFID cards that happen to walk by.

Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data. RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale.
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.
By understanding the basics of RFID technology, comprehending the threats posed by RFID hacking, and implementing robust protection strategies, organizations can safeguard their RFID systems and protect their valuable assets and sensitive information from . By closely monitoring the power consumption levels of RFID tags, hackers can fool your systems. With some ingenuity and a cell phone bad actors can perform an RFID hack that will steal sensitive information or breach secured areas.
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
These often-overlooked security checkpoints have multiple weaknesses that adversaries could exploit to gain illegitimate access to your physical environment. This post covers the technical details of two common attack methods for RFID credential theft.Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain unauthorized access to buildings and other secure areas.With the recent shift to contactless payment cards, more cybercriminals are turning to RFID credit card theft via scanning. This article will explain how this theft happens and provide tips on how to protect your RFID credit card from potential thefts and other common payment card frauds.
RFID scanners that capture and record ID information are certainly not legal, but for those with the proper skills, they’re easy to build. Hackers use a long-range reader to silently steal this ID info from any RFID cards that happen to walk by.Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on sensitive data. Second, attackers can use a high-powered reader to forcibly power up a tag that has been turned off to steal its data.
auburn football xm radio
RFID theft occurs when someone uses their own RFID reader to trigger the chip in your credit card; a process called ‘skimming’ or ‘digital pickpocketing.’ The card thinks it is being asked for information to carry out a sale. The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and can sniff and log.

rfid hacking speed
rfid hacking
wiki nfc receiver for credit cards
rfid card hacked
Here is everything you need to know in order to listen to Auburn football games on the radio this season. Auburn football radio station 2024. Radio station: WGZZ 94.3 FM, .Fans can listen to free, live streaming audio of Auburn Sports Network radio broadcasts of Tiger games and coach's shows. Computer; Mobile App; Radio; TuneIn Opens .
rfid hacking card steal|how to keep rfid from hacking