rfid chip purpose In this definition, learn what an operating systems is, how it works and manages all application programs in a computer, and about the types and functions of OSes. Reading NFC tags with the iPhone 7, 8 or X will depend on your version of operating system as follows : iOS 14 : If you have the latest iOS 14 operating system, you can read NFC tags natively with the built-in reader. Just .
0 · what does rfid stand for
1 · rfid what does it mean
2 · rfid is involved when using
3 · rfid explained
4 · radio frequency identification tags are
5 · how do rfid work
6 · how do rfid chips work
7 · does 911 use rfids
El chip está en la parte interna superior del iPhone. Esta ubicación es muy acertada, puesto que facilita enormemente su uso en la vida cotidiana. Como te podrás imaginar, es mucho más fácil acercar la parte de arriba del .
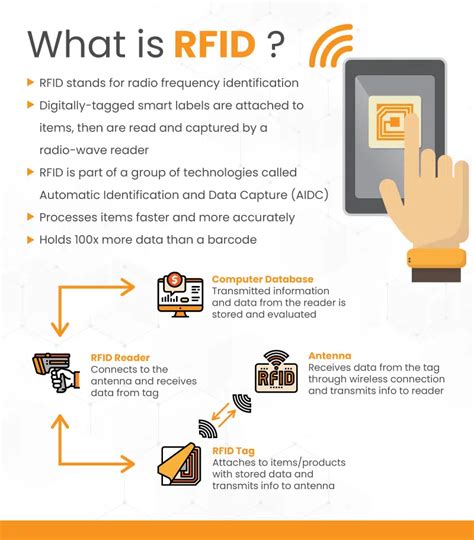
RFID (radio frequency identification) is a form of wireless communication that incorporates the use of electromagnetic or electrostatic coupling in the radio frequency portion of the electromagnetic spectrum to uniquely identify an object, animal or person.What is the purpose of RFID identification, and what access control problems and security risks are associated with it? RFID stands for radio frequency identification. RFID tags emit radio si.
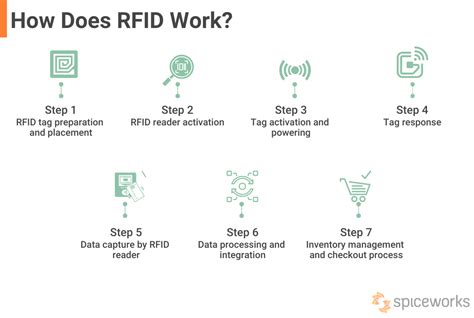
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder called a tag, a radio receiver, and a transmitter. When triggered by an electromagnetic interrogation pulse from a nearby RFID reader device, the tag transmits digital data, usually an identifying inventory number, back to the reader. This number can be used to track inventory goods.Information security threats. Mitigating information security threats is an ongoing battle. Here you'll find information on the latest malware and cyberattacks facing enterprises, from viruses and .In this definition, learn what an operating systems is, how it works and manages all application programs in a computer, and about the types and functions of OSes.
User authentication verifies the identity of a user attempting to gain access to a network or computing resource by authorizing a human-to-machine transfer of credentials during interactions on a .Three-factor authentication (3FA) is the use of identity-confirming credentials from three separate categories of authentication factors -- typically, the knowledge, possession and inherence .Gaining ISO 27002 certification can be a daunting process, so what auditing tools can help? David Mortman weighs in on how to choose the best auditing tool for your organization.
advanced persistent threat (APT) An advanced persistent threat (APT) is a prolonged and targeted cyber attack in which an intruder gains access to a network and remains undetected for an extended .Information security threats. Mitigating information security threats is an ongoing battle. Here you'll find information on the latest malware and cyberattacks facing enterprises, from viruses and .In this definition, learn what an operating systems is, how it works and manages all application programs in a computer, and about the types and functions of OSes.
User authentication verifies the identity of a user attempting to gain access to a network or computing resource by authorizing a human-to-machine transfer of credentials during interactions on a .
what does rfid stand for
Three-factor authentication (3FA) is the use of identity-confirming credentials from three separate categories of authentication factors -- typically, the knowledge, possession and inherence .Gaining ISO 27002 certification can be a daunting process, so what auditing tools can help? David Mortman weighs in on how to choose the best auditing tool for your organization.
rfid what does it mean
I have LibNFC working from the Linux terminal recognising my ACR122U Reader, and I wanted to know if there was a method for it to work through Chrome on a Linux Desktop as it is really .
rfid chip purpose|does 911 use rfids