what is a rfid ghost read A Ghost tag read, or simply Ghost read, is the reception by the reader of an apparently valid series of tag communications that is decoded into an identifier that is not stored on any tag in the reader’s communication zone. It depends on the type of tag. You can try NFC Tools or the MiFare Classic Tool to emulate cards from your phone, but in my experience it's too limited. NFC tools can emulate tags but I've .
0 · what is rfid skimming
1 · what is rfid identification
2 · rfid wallet scam
3 · rfid skimming scam
4 · rfid scam
5 · rfid chip scanning
6 · rfid chip
Write better code with AI Code review. Manage code changes
This work introduces performance metrics to solve RFID reader problems and proposes three solutions: the Minimum Overlapped Read Zone (MORZ) with Received Signal Strength Indicator (RSSI), the Spatial-Temporal Division Access (STDA) method, and double bigger size of tags .A Ghost tag read, or simply Ghost read, is the reception by the reader of an apparently valid .
This work introduces performance metrics to solve RFID reader problems and proposes three solutions: the Minimum Overlapped Read Zone (MORZ) with Received Signal Strength Indicator (RSSI), the Spatial-Temporal Division Access (STDA) method, and double bigger size of tags attached on the object.A Ghost tag read, or simply Ghost read, is the reception by the reader of an apparently valid series of tag communications that is decoded into an identifier that is not stored on any tag in the reader’s communication zone.An all Atmel HF component secure RFID starter kit for prototyping and developing secure RFID applications. It features industry’s lowest BOM count and small footprint reader reference design. What Is RFID Skimming—and Should I Worry About It? Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal .
what is rfid skimming
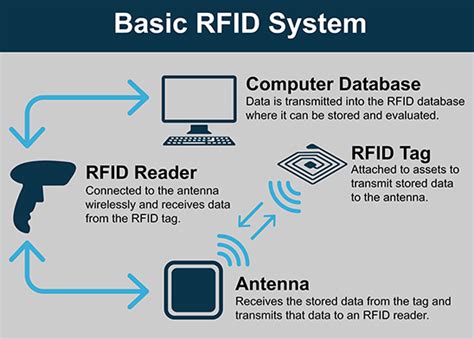
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder called a tag, a radio receiver, and a transmitter. Learn how to effectively read RFID tags and unlock their full potential. Discover the tools, techniques, and benefits of RFID technology in this comprehensive guide.RFID is an acronym for Radio Frequency Identification which means RFID is the wireless, non-contact use of radio frequency waves to transfer data and identify objects, animals, or humans. RFID systems are usually comprised of an RFID reader, RFID tags, and antennas.
atm contactless card reader
RFID (Radio Frequency Identification) is a technology that uses electromagnetic fields to automatically identify and track tags attached to objects. These tags contain electronically stored information that can be read from several meters away, without requiring direct line-of .The RFID reader is a network-connected device that can be portable or permanently attached. It uses radio waves to transmit signals that activate the tag. Once activated, the tag sends a wave back to the antenna, where it is translated into data. The transponder is in the RFID tag itself. What is RFID? RFID stands for Radio Frequency IDentification. RFID is an abbreviation that refers to any electronic device that uses radio waves to facilitate the communication of data for the purpose of identification, and sometimes to locate and/or sense the condition (s), of animate and inanimate objects."This work introduces performance metrics to solve RFID reader problems and proposes three solutions: the Minimum Overlapped Read Zone (MORZ) with Received Signal Strength Indicator (RSSI), the Spatial-Temporal Division Access (STDA) method, and double bigger size of tags attached on the object.
what is rfid identification
A Ghost tag read, or simply Ghost read, is the reception by the reader of an apparently valid series of tag communications that is decoded into an identifier that is not stored on any tag in the reader’s communication zone.An all Atmel HF component secure RFID starter kit for prototyping and developing secure RFID applications. It features industry’s lowest BOM count and small footprint reader reference design. What Is RFID Skimming—and Should I Worry About It? Some security experts have voiced concerns about a phenomenon called RFID skimming, in which a thief with an RFID reader may be able to steal your credit card number or personal .
Radio-frequency identification (RFID) uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of a tiny radio transponder called a tag, a radio receiver, and a transmitter. Learn how to effectively read RFID tags and unlock their full potential. Discover the tools, techniques, and benefits of RFID technology in this comprehensive guide.
RFID is an acronym for Radio Frequency Identification which means RFID is the wireless, non-contact use of radio frequency waves to transfer data and identify objects, animals, or humans. RFID systems are usually comprised of an RFID reader, RFID tags, and antennas. RFID (Radio Frequency Identification) is a technology that uses electromagnetic fields to automatically identify and track tags attached to objects. These tags contain electronically stored information that can be read from several meters away, without requiring direct line-of .
The RFID reader is a network-connected device that can be portable or permanently attached. It uses radio waves to transmit signals that activate the tag. Once activated, the tag sends a wave back to the antenna, where it is translated into data. The transponder is in the RFID tag itself.
are contactless payment cards safe
rfid wallet scam
allahabad bank contactless card
american express blue card contactless
Go to Settings: Open the Settings app on your iPhone 6 by tapping on the gear icon on your home screen. 2. Navigate to the NFC settings: Scroll down the settings menu and look for the “Wallet & Apple Pay” option. .
what is a rfid ghost read|rfid scam