secure symmetric authentication for rfid tags ppt download Ø Numerous authentication protocols for RFID systems were proposed in an attempt to . TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of the Tigers, Andy Burcham, weekly guests will include head football coach Hugh Freeze in the fall .
0 · Securing IoT
1 · Secure symmetric authentication for RFID tags
2 · Secure Symmetric Authentication for RFID Tags
3 · Secure Symmetric Authentication for RFID Tags
4 · SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
5 · Presentation On SECURE SYMMETRIC AUTHENTICATION
6 · (PPTX) Presentation On SECURE SYMMETRIC
NFC tag reader is an NFC device that works in NFC reader or writer mode, which enables this NFC device to read information stored on inexpensive NFC tags embedded in labels or smart posters. To make the NFC .
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to .The three main security threats in RFID systems are forgery of tags, unwanted tracking of .
The three main security threats in RFID systems are forgery of tags, unwanted tracking of .In this paper, we demonstrate how the project ART (Authentication for long-range RFID . Targeting RFID tag with short tag ID, we employ a resource friendly symmetric .
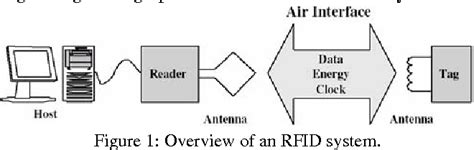
Starting with a short introduction into common RFID systems with passive tags, we present a . Recently, many solutions were proposed to secure RFID systems and many .The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.
Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableStarting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.

Recently, many solutions were proposed to secure RFID systems and many such systems are based on only lightweight primitives, including symmetric encryption, hash functions, and exclusive OR operation.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.
Securing IoT
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
nfc card logo
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.
Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableStarting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
Secure symmetric authentication for RFID tags
Secure Symmetric Authentication for RFID Tags
NFC tags are passive data stores that can be read and under some circumstances written to, by an NFC device. Typically, they contain data and are read-only in normal use, but may be rewritable. Apps include secure .
secure symmetric authentication for rfid tags ppt download|Securing IoT