kali brute force rfid reader Place „Magic” card on the reader, set new UID root@kali:~# nfc-mfsetuid 3c3df10d NFC reader: pn532_uart:/dev/ttyUSB0 opened Sent bits: 26 (7 bits) Received bits: 04 00 Sent bits: 93 20 . Auburn Football - Get all the Auburn football radio you could need, with TuneIn. You can listen to our Auburn football radio station anywhere in the country. Get all your news about Auburn football and listen live when a game is on. Just check .
0 · rfdump
1 · matamorphosis/MFRC522RFIDPyAuthKeyBruteforcer
2 · libnfc
3 · Sławomir Jasek
4 · RFID Hacking with The Proxmark 3
5 · MCT BruteForce Mod V3
6 · Is there a way to bruteforce find an rfid tag for a reader?
7 · Hacking our first MIFAR/RFID Tag
8 · Cracking Mifare Classic cards with Proxmark3 RDV4
9 · #pentestips installing libnfc on Kali linux. — Lab401
Your Country Leader. WHEP. Radio Baldwin. Q-94. America's Best Country. WRWW. The Red Arrow Sports Network. Listen to Stream Auburn Tigers (Football) here on TuneIn! Listen .
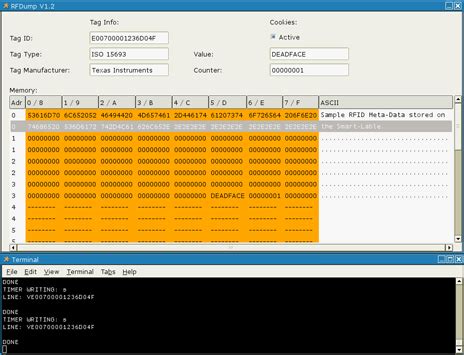
RFDump is a tool to decode RFID tags and show their meta information: tag ID, tag type, manufacturer etc. The user data memory of a tag can be displayed and modified using either a .If it's an entry code to a building with multiple entrances, each with their own RFID reader, you can split the bruteforce set over all of them and reduce the required time by the number of .It's a simple matter to scan an existing working card and create a clone. With a high powered reader, one can steal RFID tags from multiple feet away. With the Tag ID in hand, we now .Place „Magic” card on the reader, set new UID root@kali:~# nfc-mfsetuid 3c3df10d NFC reader: pn532_uart:/dev/ttyUSB0 opened Sent bits: 26 (7 bits) Received bits: 04 00 Sent bits: 93 20 .
libnfc is a library for Near Field Communication. It abstracts the low-level details of communicating with the devices away behind an easy-to-use high-level API. It supports most hardware based . My tool of choice (and quite frankly a go-to tool for any RFID-related research) is a Proxmark3 RDV4 bought from Lab401. It’s a great tool capable of reading, writing, brute .
This tool provides several features to interact with Mifare Classic RFID-Tags and Mifare Ultralight RFID-Tags. It is designed for users who have at least basic familiarity with the . LibNFC is the fundamental tool for RFID manipulation on Windows/Linux/macOS. It is a mature suite of tools that provide read/write/emulate functionality for high-frequency RFID .Choose the descending pure brute force option, or use the file option and provide a file with the default key. You should get a response like the following: Feel free to pull this code, and get in .RFDump is a tool to decode RFID tags and show their meta information: tag ID, tag type, manufacturer etc. The user data memory of a tag can be displayed and modified using either a hex or an ASCII editor.
What’s covered can be done with a simple RFID card reader found on Amazon for ~30€ (~35$). Mine was the [easyazon_link identifier=”B07FCLY4S9″ locale=”US” tag=”hackm01-20″]ACS ACR122U [/easyazon_link] simply because it was the most mentioned one on a few forums and blog posts I had read at the time. If it's an entry code to a building with multiple entrances, each with their own RFID reader, you can split the bruteforce set over all of them and reduce the required time by the number of accessible readers. 12 days for 4 entrances, just over a week for 6 entrances.It's a simple matter to scan an existing working card and create a clone. With a high powered reader, one can steal RFID tags from multiple feet away. With the Tag ID in hand, we now need a blank RFID card that we can clone the Tag ID onto.Place „Magic” card on the reader, set new UID root@kali:~# nfc-mfsetuid 3c3df10d NFC reader: pn532_uart:/dev/ttyUSB0 opened Sent bits: 26 (7 bits) Received bits: 04 00 Sent bits: 93 20 Received bits: 0c 5c ee 0d b3 Sent bits: 93 70 0c 5c ee 0d b3 5c c2 (.)
libnfc is a library for Near Field Communication. It abstracts the low-level details of communicating with the devices away behind an easy-to-use high-level API. It supports most hardware based on the NXP PN531, PN532 or PN533 controller chips.
rfdump
matamorphosis/MFRC522RFIDPyAuthKeyBruteforcer
My tool of choice (and quite frankly a go-to tool for any RFID-related research) is a Proxmark3 RDV4 bought from Lab401. It’s a great tool capable of reading, writing, brute-forcing, emulation. This tool provides several features to interact with Mifare Classic RFID-Tags and Mifare Ultralight RFID-Tags. It is designed for users who have at least basic familiarity with the Mifare Classic technology.

LibNFC is the fundamental tool for RFID manipulation on Windows/Linux/macOS. It is a mature suite of tools that provide read/write/emulate functionality for high-frequency RFID cards, covering ISO/IEC 14443 A and B, FeliCa & Jewel/Topaz.
Choose the descending pure brute force option, or use the file option and provide a file with the default key. You should get a response like the following: Feel free to pull this code, and get in running with other RFID reader libraries, I'd love to turn .RFDump is a tool to decode RFID tags and show their meta information: tag ID, tag type, manufacturer etc. The user data memory of a tag can be displayed and modified using either a hex or an ASCII editor. What’s covered can be done with a simple RFID card reader found on Amazon for ~30€ (~35$). Mine was the [easyazon_link identifier=”B07FCLY4S9″ locale=”US” tag=”hackm01-20″]ACS ACR122U [/easyazon_link] simply because it was the most mentioned one on a few forums and blog posts I had read at the time.
If it's an entry code to a building with multiple entrances, each with their own RFID reader, you can split the bruteforce set over all of them and reduce the required time by the number of accessible readers. 12 days for 4 entrances, just over a week for 6 entrances.It's a simple matter to scan an existing working card and create a clone. With a high powered reader, one can steal RFID tags from multiple feet away. With the Tag ID in hand, we now need a blank RFID card that we can clone the Tag ID onto.Place „Magic” card on the reader, set new UID root@kali:~# nfc-mfsetuid 3c3df10d NFC reader: pn532_uart:/dev/ttyUSB0 opened Sent bits: 26 (7 bits) Received bits: 04 00 Sent bits: 93 20 Received bits: 0c 5c ee 0d b3 Sent bits: 93 70 0c 5c ee 0d b3 5c c2 (.)
libnfc is a library for Near Field Communication. It abstracts the low-level details of communicating with the devices away behind an easy-to-use high-level API. It supports most hardware based on the NXP PN531, PN532 or PN533 controller chips. My tool of choice (and quite frankly a go-to tool for any RFID-related research) is a Proxmark3 RDV4 bought from Lab401. It’s a great tool capable of reading, writing, brute-forcing, emulation. This tool provides several features to interact with Mifare Classic RFID-Tags and Mifare Ultralight RFID-Tags. It is designed for users who have at least basic familiarity with the Mifare Classic technology.
LibNFC is the fundamental tool for RFID manipulation on Windows/Linux/macOS. It is a mature suite of tools that provide read/write/emulate functionality for high-frequency RFID cards, covering ISO/IEC 14443 A and B, FeliCa & Jewel/Topaz.

libnfc

copy access card to phone nfc
Nothing beats a Saturday listening to Auburn Sports Network’s all-day coverage of Auburn Tigers football in the fall. This season’s lineup within the Auburn Sports Network changes slightly, as Andy Burcham will be joined by .
kali brute force rfid reader|RFID Hacking with The Proxmark 3