smart card network security A smart card is a physical card that has an embedded integrated chip that acts as a security token. Smart cards are typically the same size as a driver's license or credit card and can be made out of metal or plastic. Get the latest version. 0.4.2. Aug 22, 2024. Older versions. Leap Top-Up is an essential application for individuals using public transportation in specific regions, offering a .
0 · windows 10 smart card setup
1 · what is smart card standards
2 · what is smart card authentication
3 · smart cards in network security
4 · smart card security system
5 · smart card identification
6 · smart card based identification system
7 · smart card based authentication
The NFL playoffs are here and Wild Card Weekend is well underway, with four of six games wrapped up over the weekend. On Saturday, action kicked off with C.J. Stroud and the Texans defeating Joe Flacco and .If you want a more efficient way to automate these shortcuts, consider investing in a set of DIMPLE Smart Buttons. These physical buttons .
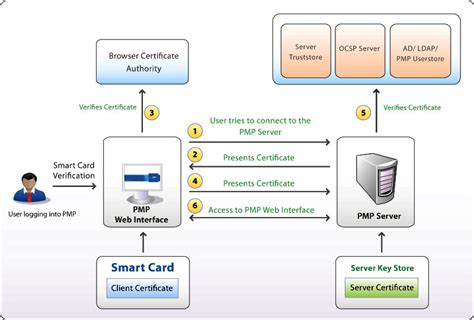
Smart card-based network security measures add extra security levels to single-factor authentication systems. A stolen password won’t work without the correct smart card to . Smart card systems have proven to be more reliable than other machine-readable cards, like magnetic strips and barcodes. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. Smart card-based network security measures add extra security levels to single-factor authentication systems. A stolen password won’t work without the correct smart card to go with it. The encryption system in smart cards ensure your credentials are safe, making them difficult to copy or modifyA smart card is a physical card that has an embedded integrated chip that acts as a security token. Smart cards are typically the same size as a driver's license or credit card and can be made out of metal or plastic.
Smartcard applications could be programmed using Java Card, an open platform from Sun Microsystems. Today, we find smartcard technology mostly used in communications (GSM/CDMA Sim Card) and payments (credit/debit card). Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations. The universal integrated circuit card (UICC) for mobile phones, installed as pluggable SIM card or embedded eSIM, is also a type of smart card. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
Smart card authentication can provide several benefits for network security, such as preventing unauthorized access to the network, protecting sensitive data on the network, simplifying the.A smart card is a security device that contains an embedded microprocessor and can securely store and process data. In cybersecurity, smart cards are often used as a form of two-factor authentication, where the card and a PIN are required to access a secure system or network.Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. They protect against a full range of security threats, from careless storage of user passwords
Smart card systems have proven to be more reliable than other machine-readable cards, like magnetic strips and barcodes. Smart cards also provide vital components of system security for the exchange of data throughout virtually any type of network. Smart card-based network security measures add extra security levels to single-factor authentication systems. A stolen password won’t work without the correct smart card to go with it. The encryption system in smart cards ensure your credentials are safe, making them difficult to copy or modifyA smart card is a physical card that has an embedded integrated chip that acts as a security token. Smart cards are typically the same size as a driver's license or credit card and can be made out of metal or plastic.
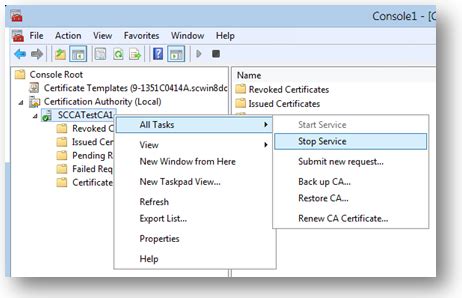
Smartcard applications could be programmed using Java Card, an open platform from Sun Microsystems. Today, we find smartcard technology mostly used in communications (GSM/CDMA Sim Card) and payments (credit/debit card). Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.

Smart cards may provide strong security authentication for single sign-on (SSO) within organizations. Numerous nations have deployed smart cards throughout their populations. The universal integrated circuit card (UICC) for mobile phones, installed as pluggable SIM card or embedded eSIM, is also a type of smart card.
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. Smart card authentication can provide several benefits for network security, such as preventing unauthorized access to the network, protecting sensitive data on the network, simplifying the.A smart card is a security device that contains an embedded microprocessor and can securely store and process data. In cybersecurity, smart cards are often used as a form of two-factor authentication, where the card and a PIN are required to access a secure system or network.
windows 10 smart card setup
what is smart card standards
The combination of the Access Card. Recently Searched Tags Documents No results found .
smart card network security|smart card based authentication