rfid cards in business security As the landscape of modern security architecture continues to evolve, RFID key cards are poised to play an increasingly significant role. With their enhanced security, convenience, and flexibility, they represent a key component of effective access control in a variety of sectors.
I also keep the key card in the back of the phone, between the case and phone as a back up. Reply reply . Tesla's RFID this isn't like normal keys used by hotels or buses where someone can clone your key. Tesla uses strong modern .
0 · vice contactless business cards
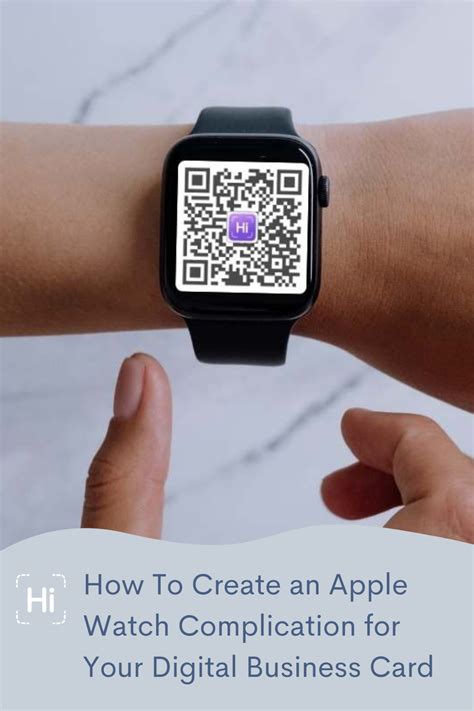
1 · rfid business card apple watch
2 · nfc contactless business card
3 · nfc business card free
4 · best virtual business card
5 · best rfid business card
6 · best nfc business card 2022
7 · best contactless business cards
Explore a wide range of our Zelda Amiibo Nfc Cards selection. Find top brands, exclusive .

Are you looking to improve business efficiency while ensuring data security? Learn how to streamline operations, enhance transparency, and protect assets by integrating RFID and blockchain.Businesses often utilize RFID access control systems to manage employee access and ensure the security of sensitive areas. By distributing RFID cards to employees, companies can .As the landscape of modern security architecture continues to evolve, RFID key cards are poised to play an increasingly significant role. With their enhanced security, convenience, and .
Are you looking to improve business efficiency while ensuring data security? Learn how to streamline operations, enhance transparency, and protect assets by integrating RFID and blockchain.Businesses often utilize RFID access control systems to manage employee access and ensure the security of sensitive areas. By distributing RFID cards to employees, companies can monitor who enters the premises and when and where in real time.As the landscape of modern security architecture continues to evolve, RFID key cards are poised to play an increasingly significant role. With their enhanced security, convenience, and flexibility, they represent a key component of effective access control in a variety of sectors. In short, RFID technology has existed for many decades, but even modern cards can pose a huge vulnerability in your RFID-based security environment if not implemented well. The main risks are that attackers can gain access to your premise through cloning, replaying, relaying and brute-force attacks.
Discover the basics of RFID cards, technology, and how RFID works. Learn about RFID tags, access control, and the ability to track and identify objects.
vice contactless business cards
RFID cards are very simple devices, which makes them reliable for everyday use. However, it also makes them an easy target for attackers looking to gain access to a facility. In this post, we’re focusing on low-power RFID cards, . Radio-frequency identification (RFID) technology is a way for retailers to identify items using radio waves. It transmits data from a RFID tag to a reader, giving you accurate, real-time tracking data of your inventory. Discover how RFID cards improve security & convenience! Explore their uses (access control, payments), benefits (increased efficiency, reduced costs), how they work, and choosing the right card. This blog aims to demystify RFID technology in ID cards, highlighting both its benefits and potential security risks, offering guidance for business leaders and decision-makers on how to.
RFID readers for a business use case, or commercial RFID door handle locks, can also rely on a high-frequency signal, with these readers operating at 13. 56 MHz and boasting a readable range of between 10 cm and 1 meter, making HF RFID much more versatile.
rfid business card apple watch
Are you looking to improve business efficiency while ensuring data security? Learn how to streamline operations, enhance transparency, and protect assets by integrating RFID and blockchain.Businesses often utilize RFID access control systems to manage employee access and ensure the security of sensitive areas. By distributing RFID cards to employees, companies can monitor who enters the premises and when and where in real time.
As the landscape of modern security architecture continues to evolve, RFID key cards are poised to play an increasingly significant role. With their enhanced security, convenience, and flexibility, they represent a key component of effective access control in a variety of sectors.
In short, RFID technology has existed for many decades, but even modern cards can pose a huge vulnerability in your RFID-based security environment if not implemented well. The main risks are that attackers can gain access to your premise through cloning, replaying, relaying and brute-force attacks. Discover the basics of RFID cards, technology, and how RFID works. Learn about RFID tags, access control, and the ability to track and identify objects.
RFID cards are very simple devices, which makes them reliable for everyday use. However, it also makes them an easy target for attackers looking to gain access to a facility. In this post, we’re focusing on low-power RFID cards, . Radio-frequency identification (RFID) technology is a way for retailers to identify items using radio waves. It transmits data from a RFID tag to a reader, giving you accurate, real-time tracking data of your inventory. Discover how RFID cards improve security & convenience! Explore their uses (access control, payments), benefits (increased efficiency, reduced costs), how they work, and choosing the right card.
smart card in bangladesh
This blog aims to demystify RFID technology in ID cards, highlighting both its benefits and potential security risks, offering guidance for business leaders and decision-makers on how to.
smart card license
nfc contactless business card
NFC/RFID skimming is where hackers/skimmers/bad guys intercept the radio wave communication between devices or simply read the radio waves that a NFC or RFID enabled device puts out. The bad guy's reader reads the data put out .
rfid cards in business security|best contactless business cards