cisco ise smart card Verify access to the ISE GUI after the Application Server service status changes to running. Super Admin User: Verify that the . See more $65.00
0 · Two Factor Authentication on ISE
1 · ISE as RADIUS server for Password + Smart Card
2 · Configure Certificate or Smartcard Based authentication for ISE
Costco Anywhere Visa Card by Citi Variable APR for purchases, balance transfers and Citi .
This document describes how to configure Client Certificate-based authentication for Identity Services Engine (ISE) management access. In this example, the ISE administrator authenticates against the User certificate to gain Admin access to the Cisco Identity Services Engine (ISE) management GUI. See moreVerify access to the ISE GUI after the Application Server service status changes to running. Super Admin User: Verify that the . See moreUse this section to configure the Client certificate or Smart Card as an external identity for administrative access to the Cisco ISE . See more The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. .
ISE and Two Factor Authentication Scenarios. ISE supports two factor authentication mechanisms using the following methods. External 2FA Identity sources (e.g. RSA Secure ID, . This document describes how to configure Client Certificate-based authentication for Identity Services Engine (ISE) management access. In this example, the ISE administrator authenticates against the User certificate to gain Admin access to the Cisco Identity Services Engine (ISE) management GUI.
The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. This document describes the components used for this setup, configuration.
ISE and Two Factor Authentication Scenarios. ISE supports two factor authentication mechanisms using the following methods. External 2FA Identity sources (e.g. RSA Secure ID, Smartcard) or any RADIUS RFC-2865 compliant token server for on or off campus support. With Cisco ISE 1.2 is it possible to enable 802.1x machine AND user smart card authentication simultaneously for wired/wireless clients (specifically Windows 7/8, but Linux or OSX would also be good). Solved: My customer have a ISE 2.2 deployment and have a test switch, what they are trying to do as you know is the continuous requests for TACACS+ access to the network from the various support and development teams. They currently use smart cards. Cisco ISE 2.7 and Windows 10 build 2004 (May 2020) added support for TEAP. This is a huge step forward because it will allow us to perform user and machine authentication at the same time. Previously, doing this required the AnyConnect NAM module and configuring EAP Chaining (Windows only).
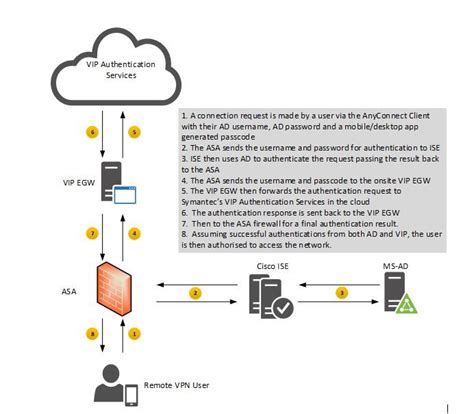
Is there a definitive guide for configuring smart card authentication on NX-OS devices that use TACACS+ on ISE? I found this white paper for IOS-XE but NX-OS is significantly different. cisco-2-factor (pragmasys.com)editor shows a smart card (PIN+ Certificate) based authentication for user and machine. EAP-FAST is the EAP method and EAP-TLS is to authenticate using certificate as inner method based on credential source used for this method. I'm preparing for a potential smart card requirement for VPN access and I'm struggling to figure out how it should work. Currently I have the ASAs sending RADIUS to ISE, which then authenticates against RSA SecurID. Cisco ISE enables an automated approach to discover, profile, authenticate, and authorize trusted endpoints and users connecting to the self-managed network infrastructure, regardless of access medium.
This document describes how to configure Client Certificate-based authentication for Identity Services Engine (ISE) management access. In this example, the ISE administrator authenticates against the User certificate to gain Admin access to the Cisco Identity Services Engine (ISE) management GUI.
The purpose of this document is to demonstrate how ISE authenticate / authorize a user that uses a smart card (PIN + Certificate) and password mechanism to login their system. This document describes the components used for this setup, configuration.ISE and Two Factor Authentication Scenarios. ISE supports two factor authentication mechanisms using the following methods. External 2FA Identity sources (e.g. RSA Secure ID, Smartcard) or any RADIUS RFC-2865 compliant token server for on or off campus support. With Cisco ISE 1.2 is it possible to enable 802.1x machine AND user smart card authentication simultaneously for wired/wireless clients (specifically Windows 7/8, but Linux or OSX would also be good). Solved: My customer have a ISE 2.2 deployment and have a test switch, what they are trying to do as you know is the continuous requests for TACACS+ access to the network from the various support and development teams. They currently use smart cards.
Cisco ISE 2.7 and Windows 10 build 2004 (May 2020) added support for TEAP. This is a huge step forward because it will allow us to perform user and machine authentication at the same time. Previously, doing this required the AnyConnect NAM module and configuring EAP Chaining (Windows only). Is there a definitive guide for configuring smart card authentication on NX-OS devices that use TACACS+ on ISE? I found this white paper for IOS-XE but NX-OS is significantly different. cisco-2-factor (pragmasys.com)editor shows a smart card (PIN+ Certificate) based authentication for user and machine. EAP-FAST is the EAP method and EAP-TLS is to authenticate using certificate as inner method based on credential source used for this method. I'm preparing for a potential smart card requirement for VPN access and I'm struggling to figure out how it should work. Currently I have the ASAs sending RADIUS to ISE, which then authenticates against RSA SecurID.
rfid based electronic passport system for easy governance using arduino
Two Factor Authentication on ISE
ISE as RADIUS server for Password + Smart Card

The problems seems to be that it's not possible to emulate/modify the sector 0, .
cisco ise smart card|Two Factor Authentication on ISE