smart card private key protection What benefits do smart cards capable of storing private keys, and devices like the YubiKey Neo (which seems to be a smart card + usb reader in a single dongle) offer above storing private keys on a plain-old usb thumb drive? View a summary of the 2016 NFL season, including standings, stats, statistics, .
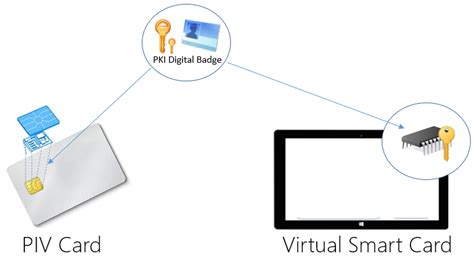
0 · Virtual Smart Card Overview
1 · Understanding and Evaluating Virtual Smart Cards
2 · Understanding Smart Card Authentication
Following points are some of the limitations of NFC technology in general. 1. It can only works in shorter distances which is about 10-20 cm. 2. It offers very low data transfer rates which is about 106 or 212 or 424 Kbps. 3. It is very expensive for the companies to . See more
To verify authorship of data, a user can sign it by using a private key stored in . Private keys in the virtual smart card are protected, not by isolation of physical memory, but by the cryptographic capabilities of the TPM. All sensitive information is encrypted by using the TPM and then stored on the hard drive in its encrypted form. To verify authorship of data, a user can sign it by using a private key stored in the virtual smart card. Digital signatures confirm the integrity and origin of the data. Storing the key in an operating system that is accessible, malicious users could access it and use it to modify already signed data or to spoof the key owner's identity The very basics. Public and private keys. Public key cryptography uses some very sophisticated mathematics to embed a secret inside a ‘private key’ from which a corresponding ‘public key’ is then generated. While related, it is generally “extremely difficult” to recreate the private key from the public key.
What benefits do smart cards capable of storing private keys, and devices like the YubiKey Neo (which seems to be a smart card + usb reader in a single dongle) offer above storing private keys on a plain-old usb thumb drive?
In TPM virtual smart cards, security is ensured with a secure key hierarchy, which includes several chains of encryption. The chain originates with the TPM storage root key, which is generated and stored within the TPM and never exposed outside the chip.Digital Identity and Security. Smart cards – An illustrated guide ( 2024) Want to know more about smart cards? Then you're in the right place. Ever thought about how that tiny piece of plastic in your wallet or phone can unlock a world of finances, identity, and communication? Using a smart card can keep your private keys safe even if your computer is compromised. Just make sure you do some research on your reader and the card you are looking to buy to make sure it will work with your OS / application.
Private keys remain securely stored on individual devices. Recent developments allow storage of FIDO keys on Android and iOS devices, known as passkeys, enhancing accessibility. Incorporates biometric authentication for heightened security and user simplicity.
user55960. Add a comment. 2 Answers. Sorted by: 3. This highly depends on the smart card. Some card simply provide a key store whereas others provide a complete infrastructure where you send your data and the smart card can sign and/or encrypt the data. The smart card is a secure token, storing the user’s private key and digital certificate securely. During a transaction, the user inserts the smart card into a reader, enters a PIN to unlock the card, and the private key stored on the card is used to sign digital transactions. Working of PKI Secure Data Transmission with Smart Cards. Private keys in the virtual smart card are protected, not by isolation of physical memory, but by the cryptographic capabilities of the TPM. All sensitive information is encrypted by using the TPM and then stored on the hard drive in its encrypted form. To verify authorship of data, a user can sign it by using a private key stored in the virtual smart card. Digital signatures confirm the integrity and origin of the data. Storing the key in an operating system that is accessible, malicious users could access it and use it to modify already signed data or to spoof the key owner's identity
The very basics. Public and private keys. Public key cryptography uses some very sophisticated mathematics to embed a secret inside a ‘private key’ from which a corresponding ‘public key’ is then generated. While related, it is generally “extremely difficult” to recreate the private key from the public key.What benefits do smart cards capable of storing private keys, and devices like the YubiKey Neo (which seems to be a smart card + usb reader in a single dongle) offer above storing private keys on a plain-old usb thumb drive? In TPM virtual smart cards, security is ensured with a secure key hierarchy, which includes several chains of encryption. The chain originates with the TPM storage root key, which is generated and stored within the TPM and never exposed outside the chip.Digital Identity and Security. Smart cards – An illustrated guide ( 2024) Want to know more about smart cards? Then you're in the right place. Ever thought about how that tiny piece of plastic in your wallet or phone can unlock a world of finances, identity, and communication?
Using a smart card can keep your private keys safe even if your computer is compromised. Just make sure you do some research on your reader and the card you are looking to buy to make sure it will work with your OS / application.
Virtual Smart Card Overview
Understanding and Evaluating Virtual Smart Cards
Private keys remain securely stored on individual devices. Recent developments allow storage of FIDO keys on Android and iOS devices, known as passkeys, enhancing accessibility. Incorporates biometric authentication for heightened security and user simplicity.
user55960. Add a comment. 2 Answers. Sorted by: 3. This highly depends on the smart card. Some card simply provide a key store whereas others provide a complete infrastructure where you send your data and the smart card can sign and/or encrypt the data.

Understanding Smart Card Authentication
View scores and results from week 4 of the 2014 NFL Postseason. Standings . .
smart card private key protection|Understanding Smart Card Authentication