smart card for authentication Learn how to use smart cards and smart card readers for authentication and remote desktop connections in Windows. Find out the requirements, services, and policies for smart card technologies. The 2022 NFL Playoff Schedule kicked off on Saturday, Jan. 14, 2023 with two Wild-Card games. In Super Bowl LVII, the Kansas City Chiefs defeated the Philadelphia Eagles 38-35 at State Farm .
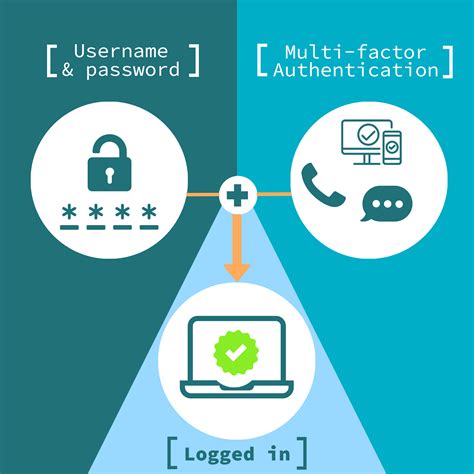
0 · smart card multi factor authentication
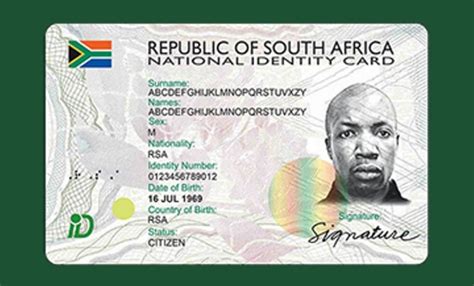
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
With one card for all your drivers’ needs, alongside comprehensive services and support, the Shell Card makes the everyday more efficient, thanks to: 60 years of experience in the fleet industry. Being widely accepted at 600,000 fuel and EV .
Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem .Learn how to use smart cards and smart card readers for authentication and remote desktop connections in Windows. Find out the requirements, services, and policies for smart card technologies. Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem architecture.Learn what a Personal Identity Verification (PIV) credential is, who is eligible for it, and how it is used for logical and physical access to federal systems and facilities. Find out the standards, features, and benefits of PIV credentials and how to test them.
smart card multi factor authentication
smart card identity
Learn how to use smart cards for authentication, digital signatures, and key exchange in Windows. This document covers smart card architecture, certificate requirements, tools, settings, and troubleshooting.Smart Card Authentication is a type of authentication that uses a physical card with a chip and a reader to verify users into enterprise resources. It is secure but expensive and requires hardware and software support.A smart card is a physical card with an embedded chip that acts as a security token. Learn how smart card authentication works, its benefits and drawbacks, and how to use it with YubiKey.
Learn how smart cards use embedded chips to verify identity and perform secure transactions. Explore the types, components, protocols, and advantages of smart card authentication, as well as the common challenges and limitations.
Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data. Learn how smart card authentication works, how to implement it, and what best practices to follow. Smart card authentication is a secure and convenient way to verify identity using a smart card with a microchip and a card reader.
union pay contactless card
smart card based identification system
suntrust contactless card
Learn how to use smart cards and smart card readers for authentication and remote desktop connections in Windows. Find out the requirements, services, and policies for smart card technologies. Learn how smart cards and smart card readers work with Windows operating system to authenticate users and applications. Explore the components and mechanisms of credential provider architecture and smart card subsystem architecture.Learn what a Personal Identity Verification (PIV) credential is, who is eligible for it, and how it is used for logical and physical access to federal systems and facilities. Find out the standards, features, and benefits of PIV credentials and how to test them. Learn how to use smart cards for authentication, digital signatures, and key exchange in Windows. This document covers smart card architecture, certificate requirements, tools, settings, and troubleshooting.
Smart Card Authentication is a type of authentication that uses a physical card with a chip and a reader to verify users into enterprise resources. It is secure but expensive and requires hardware and software support.
A smart card is a physical card with an embedded chip that acts as a security token. Learn how smart card authentication works, its benefits and drawbacks, and how to use it with YubiKey. Learn how smart cards use embedded chips to verify identity and perform secure transactions. Explore the types, components, protocols, and advantages of smart card authentication, as well as the common challenges and limitations.Certificate-based authentication is an encrypted method that enables devices and people to identify themselves to other devices and systems. Two common examples are a smart card or when an employee’s device sends a digital certificate to a network or server.
Smart card authentication is a security technology that uses smart cards, which are small plastic cards with embedded microchips, to prove a user's identity. The microchip securely stores the user's authentication credentials, such as a personal identification number (PIN), digital certificates, and biometric data.
smart card authentication step by
square contactless and chip reader hsa cards
Here's how the NFL playoffs bracket looks: AFC: The AFC divisional-round matchups are locked in. No. 4 Houston Texans at No. 1 Baltimore Ravens. No. 3 Kansas City .
smart card for authentication|authenticate using your smart card