smart card authentication key How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Pay 2.5% for all major credit cards and just 0.75% + 7¢ per INTERAC chip and PIN or tap. . (NFC) cards, Apple Pay and Google Pay. See it on your counter. Get a sneak peek at how .
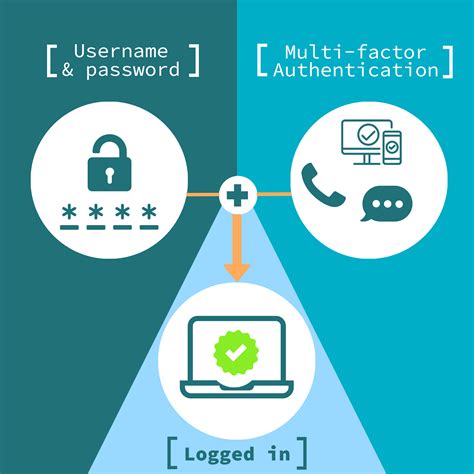
0 · smart card multi factor authentication
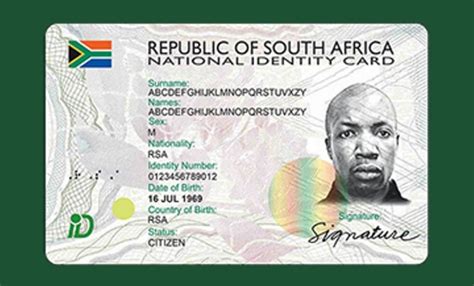
1 · smart card identity
2 · smart card based identification system
3 · smart card authentication step by
4 · smart card authentication protocol
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
The card checker will not show details for anyone under 18 years of age. Contact the relevant card scheme helpline: CISRS (scaffolding) on 0300 999 1177 option 1, then option 2 CPCS .
Vendors provide smart cards and smart card readers, and in many cases the vendors are different for the smart card and the smart card reader. Drivers for smart . See more
Best Products. Security. The Best Hardware Security Keys for 2024. Protecting your online accounts from being taken over by bad guys is critical, and a hardware security key is one of the best. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Smart cards provide: Tamper-resistant storage for protecting private keys and other forms of personal information; Isolation of security-critical computations that involve authentication, digital signatures, and key exchange from other parts of the computer. These computations are performed on the smart card
A PKI smart card is a smart card device that supports the requirements of PKI, which typically means the ability to generate, store and use asymmetric encryption keys (i.e. RSA and/or ECC). How does a smart card provide two factor authentication?YubiKey 5 Series is the most versatile security key supporting multiple authentication protocols including FIDO2/Authn (hardware bound passkey), FIDO U2F, Yubico OTP, OATH-TOTP, OATH-HOTP, Smart card (PIV) and OpenPGP. Durable and reliable. High quality design and resistant to tampering, water, and crushing.
YubiKey provides baseline functionality to authenticate as a PIV-compliant smart card out-of-the-box on Microsoft Windows Server 2008 R2 and later servers, and Microsoft Windows 7 and later clients. Authentication Steps: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card and asks the user to enter a password number or use their body marks to prove who they are.
USB smart cards like Yubikey embed the reader, and work like regular PIV cards. Each smart card is expected to contain an X.509 certificate and the corresponding private key to be used for authentication.
For sign-in to work in a smart card-based domain, the smart card certificate must meet the following conditions: The KDC root certificate on the smart card must have an HTTP CRL distribution point listed in its certificate; The smart card sign-in certificate must have the HTTP CRL distribution point listed in its certificateChapter 1. Understanding smart card authentication. Copy link. Authentication based on smart cards is an alternative to passwords. You can store user credentials on a smart card in the form of a private key and a certificate, and special software and hardware is used to access them. Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. Smart cards provide: Tamper-resistant storage for protecting private keys and other forms of personal information; Isolation of security-critical computations that involve authentication, digital signatures, and key exchange from other parts of the computer. These computations are performed on the smart cardA PKI smart card is a smart card device that supports the requirements of PKI, which typically means the ability to generate, store and use asymmetric encryption keys (i.e. RSA and/or ECC). How does a smart card provide two factor authentication?YubiKey 5 Series is the most versatile security key supporting multiple authentication protocols including FIDO2/Authn (hardware bound passkey), FIDO U2F, Yubico OTP, OATH-TOTP, OATH-HOTP, Smart card (PIV) and OpenPGP. Durable and reliable. High quality design and resistant to tampering, water, and crushing.
YubiKey provides baseline functionality to authenticate as a PIV-compliant smart card out-of-the-box on Microsoft Windows Server 2008 R2 and later servers, and Microsoft Windows 7 and later clients. Authentication Steps: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card and asks the user to enter a password number or use their body marks to prove who they are.USB smart cards like Yubikey embed the reader, and work like regular PIV cards. Each smart card is expected to contain an X.509 certificate and the corresponding private key to be used for authentication. For sign-in to work in a smart card-based domain, the smart card certificate must meet the following conditions: The KDC root certificate on the smart card must have an HTTP CRL distribution point listed in its certificate; The smart card sign-in certificate must have the HTTP CRL distribution point listed in its certificate
smart card multi factor authentication

auburn football radio fm

Custom Animal Crossing Amiibo Cards. ALL Series are Available in our store. .
smart card authentication key|smart card multi factor authentication