relay attack contactless cards Most of the attacks discovered against contactless payments work on top of the relay attack. The identified security issues result from flawed implementation of the standard. . 1. Do not use the NFC UID for any security purpose, as you can see a phone does give a random one for privacy purposes. The NFC UID is designed only to help reading .
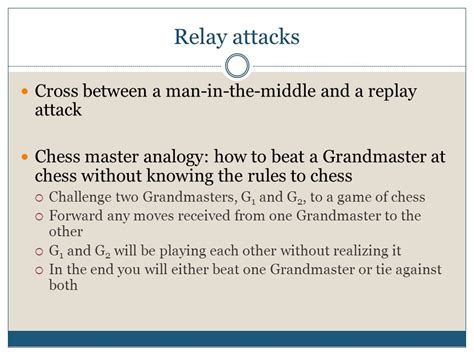
0 · relay attack grandmaster
1 · relay attack
2 · example of a relay attack
Shop Target for nintendo 3ds nfc reader you will love at great low prices. Choose from Same .
Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction. Most of the attacks discovered against contactless payments work on top of the relay attack. The identified security issues result from flawed implementation of the standard. .Security experts have shown that attackers can intercept and relay signals between a contactless payment card or mobile device and the payment terminal. This enables unauthorized . Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction. .
relay attack grandmaster
relay attack
Although convenient, contactless payments are vulnerable to relay attacks that enable attackers to execute fraudulent payments. A number of countermeasures have been proposed to . Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction. Most of the attacks discovered against contactless payments work on top of the relay attack. The identified security issues result from flawed implementation of the standard. .
Security experts have shown that attackers can intercept and relay signals between a contactless payment card or mobile device and the payment terminal. This enables unauthorized .
Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction. .Although convenient, contactless payments are vulnerable to relay attacks that enable attackers to execute fraudulent payments. A number of countermeasures have been proposed to . Three examples of relay attacks. Vehicle relay theft; SMB (Server Message Block) relay attack; Contactless card attacks; 1. Vehicle relay theft. When cars are the target, relay .
q18 smart watch sim card
example of a relay attack
pc/sc ccid iso 7816 usb smart card reader
fully executed a relay attack against an ISO 14443A contactless smart card, up to a distance of 50 m. Simply relaying information between the card and reader over a longer distance does not . In this paper we show that there is the potential for practical and powerful frauds against contactless cards relying on relay attacks extended with some logic. The frauds could . Commonly used in the context of keyless entry systems, contactless payments, or garage door openers, a relay attack involves capturing signals from a legitimate device, such . Elements of the payment card industry have introduced a new contactless payment card security feature, designed to defend against relay attacks. Relay attacks were first .
Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction.
Most of the attacks discovered against contactless payments work on top of the relay attack. The identified security issues result from flawed implementation of the standard. .Security experts have shown that attackers can intercept and relay signals between a contactless payment card or mobile device and the payment terminal. This enables unauthorized . Both are vulnerable to what’s called a relay attack. The risk for contactless cards, however, is far higher because no PIN number is required to complete the transaction. .
Although convenient, contactless payments are vulnerable to relay attacks that enable attackers to execute fraudulent payments. A number of countermeasures have been proposed to . Three examples of relay attacks. Vehicle relay theft; SMB (Server Message Block) relay attack; Contactless card attacks; 1. Vehicle relay theft. When cars are the target, relay .fully executed a relay attack against an ISO 14443A contactless smart card, up to a distance of 50 m. Simply relaying information between the card and reader over a longer distance does not .
In this paper we show that there is the potential for practical and powerful frauds against contactless cards relying on relay attacks extended with some logic. The frauds could .
Commonly used in the context of keyless entry systems, contactless payments, or garage door openers, a relay attack involves capturing signals from a legitimate device, such .
samsung smart tv sd card slot

relay attack contactless cards|relay attack