attacks on smart cards pdf information from cryptosystems such as smart cards. All concepts are progressively introduced, mathematically analyzed and illustrated using many real attacks results. The main attack . You’ll need an NFC tag-writing app to set up the tags, such as the NFC Writer by Trigger app. Once programmed, you can tap any NFC-enabled device on the tag and take advantage of its benefits.
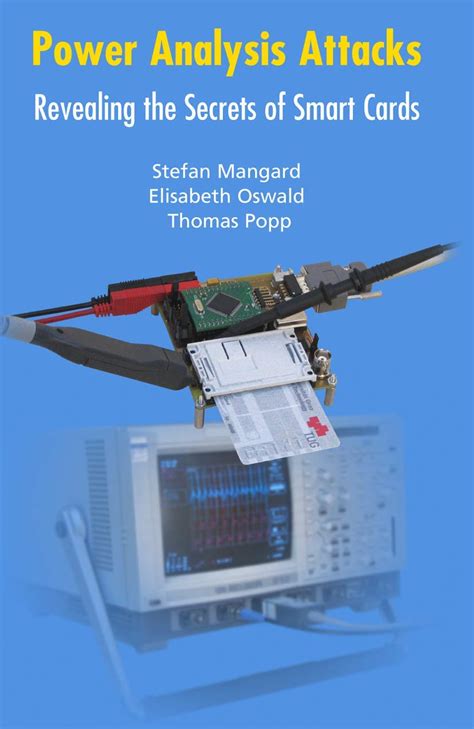
0 · \Power Analysis Attacks: Revealing the Secrets of Smart Cards"
1 · [PDF] Known Attacks against Smartcards
2 · Power Analysis Attacks: Revealing the Secrets of Smart Cards
3 · Known Attacks Against Smartcards jack
4 · Examining smart
5 · Application of Attack Potential to Smartcards and Similar
6 · A taxonomy of various attacks on smart card–based applications
7 · (PDF) “Internet of Smart Cards”: a Pocket Attacks Scenario
8 · (PDF) Smart Card Security
Setting up NFC cards on the Nintendo Switch is a straightforward process. Follow these steps to get started: Step 1: Enable NFC on your Nintendo Switch Ensure that NFC is enabled on . See more
information from cryptosystems such as smart cards. All concepts are progressively introduced, mathematically analyzed and illustrated using many real attacks results. The main attack .
Power analysis attacks allow the extraction of secret information from smart cards. Smart cards are used in many applications including banking, mobile communications, pay .
\Power Analysis Attacks: Revealing the Secrets of Smart Cards"
[PDF] Known Attacks against Smartcards
This document analyzes, from a technical point of view, currently known attacks against smart card implementations. The purpose of this analysis is to give the necessary background for the . In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.The first comprehensive discussion of power analysis attacks on smart cards. Examples and case studies illustrate the various attacks, from simple to differential power-analysis attacks. .experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the complete attack could realistically be .
This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their .This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their countermeasures, and covers . Infecting several phones an attacker could have under his control a large set of cards, a sort of “Internet of Smart Cards”. We show that surveying a decade of research and .This paper examines how monitoring power consumption signals might breach smart-card security. Both simple power analysis and differential power analysis attack.
information from cryptosystems such as smart cards. All concepts are progressively introduced, mathematically analyzed and illustrated using many real attacks results. The main attack methods and some variants are presented. Standard countermeasures used to protect cryptosystems against power analysis attacks are also presented. Limitations and e - Power analysis attacks allow the extraction of secret information from smart cards. Smart cards are used in many applications including banking, mobile communications, pay TV, and electronic.This document analyzes, from a technical point of view, currently known attacks against smart card implementations. The purpose of this analysis is to give the necessary background for the assessment of the mechanisms that can enhance the security of smart cards.
In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.The first comprehensive discussion of power analysis attacks on smart cards. Examples and case studies illustrate the various attacks, from simple to differential power-analysis attacks. Detailed descriptions and comparisons of the effectiveness of different countermeasures.experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the complete attack could realistically be carried out.
This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their countermeasures. In addition, it covers some of the open source tools available for .This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their countermeasures, and covers some of the open source tools available for its development. Infecting several phones an attacker could have under his control a large set of cards, a sort of “Internet of Smart Cards”. We show that surveying a decade of research and development in the.This paper examines how monitoring power consumption signals might breach smart-card security. Both simple power analysis and differential power analysis attack.
Power Analysis Attacks: Revealing the Secrets of Smart Cards
information from cryptosystems such as smart cards. All concepts are progressively introduced, mathematically analyzed and illustrated using many real attacks results. The main attack methods and some variants are presented. Standard countermeasures used to protect cryptosystems against power analysis attacks are also presented. Limitations and e - Power analysis attacks allow the extraction of secret information from smart cards. Smart cards are used in many applications including banking, mobile communications, pay TV, and electronic.This document analyzes, from a technical point of view, currently known attacks against smart card implementations. The purpose of this analysis is to give the necessary background for the assessment of the mechanisms that can enhance the security of smart cards. In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.
The first comprehensive discussion of power analysis attacks on smart cards. Examples and case studies illustrate the various attacks, from simple to differential power-analysis attacks. Detailed descriptions and comparisons of the effectiveness of different countermeasures.experiments to identify the full attack, provided it is clear that the attack actually proves that access has been gained to a TOE asset, and that the complete attack could realistically be carried out.
This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their countermeasures. In addition, it covers some of the open source tools available for .
This survey discusses smart card technology in detail and provides a comprehensive taxonomy of security attacks on smart card–based applications and their countermeasures, and covers some of the open source tools available for its development. Infecting several phones an attacker could have under his control a large set of cards, a sort of “Internet of Smart Cards”. We show that surveying a decade of research and development in the.

![[PDF] Known Attacks against Smartcards](/upluds/images/[PDF] Known Attacks against Smartcards .jpg)
Known Attacks Against Smartcards jack
Examining smart
Application of Attack Potential to Smartcards and Similar
A taxonomy of various attacks on smart card–based applications
Actually making them. It’s very simple. Activate NFC on your phone. Make sure you have the unfixed-info and locked-secret bins already loaded in (reference the guide above for help). Open Tagmo, and press “Load .
attacks on smart cards pdf|(PDF) Smart Card Security