smart card security pdf This white paper was developed by the Smart Card Alliance to describe the role of smart card technology in enhancing the security of FIDO implementations. The white paper includes the . NFC-enabled devices and payment readers exchange payment data using unique, one-time codes instead of actual card numbers. This encryption makes NFC payments vastly more secure than swiping the .It feels like the obvious answer is no, but I've been seeing these bootleg cards showing up on every selling site I see and I'm wondering why they've been able ti day around, being produced by people, for this long. Selling cards preloaded with data is definitely illegal. Selling an nfc .
0 · Smart Cards, Tokens, Security and Applications
1 · Smart Card Technology and the FIDO Protocols
2 · Smart Card Security; Technology and Adoption
3 · Smart Card Security and Applications, Second Edition
4 · Smart Card Security
5 · Smart Card Handbook
6 · Smart Card Authentication for Mobile Devices
7 · Smart Card & Security Basics
8 · Chapter 1 An Introduction to Smart Cards
9 · (PDF) Smart Card Security; Technology and Adoption
10 · (PDF) Smart Card Security
NFC creator is a smaller app that focuses on writing various NDEF messages to .
In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.The multifunctional role of smart card particularly in security provision ranges .
SECURITY OF SMART CARDS. Smart cards are mostly used in security applications. Smart cards offer much higher security compared to basic printed cards, and even magnetic stripe . The multifunctional role of smart card particularly in security provision ranges from user identification to authentication for physical and logical access control to protected resources.This white paper was developed by the Smart Card Alliance to describe the role of smart card technology in enhancing the security of FIDO implementations. The white paper includes the .range of smart cards and tokens, considering the various types, capabilities, popular applications and the practicality of their development and deployment, covered in detail within subsequent .
This paper describes two novel types of smart card with unconventional form factors, designed to take advantage of common interfaces built into many current handheld devices. Keywords: .
In addition to information security, smart cards achieve greater physical security of services and equipment, because the card restricts access to all but the authorized user(s). E-mail and PCs .
This chapter provides a synopsis of the essential principles, methods and strategies for producing secure smart cards and secure smart card applications. The primary problem faced by all .Revised and updated edition with new content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking cards, identity cards or passports, .From user authentication in remote payments, Internet transactions, and telephony - to fraud and counterfeit in card payments - to electronic ticketing, portability, and confidentiality, this .
In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.SECURITY OF SMART CARDS. Smart cards are mostly used in security applications. Smart cards offer much higher security compared to basic printed cards, and even magnetic stripe cards. Smart cards are often used to prove identity, control access to protected areas, or guarantee payments.
The multifunctional role of smart card particularly in security provision ranges from user identification to authentication for physical and logical access control to protected resources.
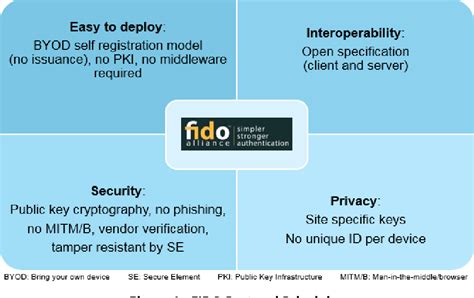
This white paper was developed by the Smart Card Alliance to describe the role of smart card technology in enhancing the security of FIDO implementations. The white paper includes the following content: An overview of the FIDO principles and protocols A description of the security benefits of using smart card technology in FIDO protocol Tokens
This paper describes two novel types of smart card with unconventional form factors, designed to take advantage of common interfaces built into many current handheld devices. Keywords: Mobile Devices, Authentication, Smart Cards.In addition to information security, smart cards achieve greater physical security of services and equipment, because the card restricts access to all but the authorized user(s). E-mail and PCs are being locked-down with smart cards.
This chapter provides a synopsis of the essential principles, methods and strategies for producing secure smart cards and secure smart card applications. The primary problem faced by all information technology systems subject to attack is the avalanche effect that often occurs after a successful attack. Classification of forms of attacks on .Revised and updated edition with new content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking cards, identity cards or passports, and mobile systems security
Smart Cards, Tokens, Security and Applications
From user authentication in remote payments, Internet transactions, and telephony - to fraud and counterfeit in card payments - to electronic ticketing, portability, and confidentiality, this comprehensive resource describes the major applications of smart cards. In this chapter, a description of the various attacks and countermeasures that apply to secure smart card applications are described.SECURITY OF SMART CARDS. Smart cards are mostly used in security applications. Smart cards offer much higher security compared to basic printed cards, and even magnetic stripe cards. Smart cards are often used to prove identity, control access to protected areas, or guarantee payments. The multifunctional role of smart card particularly in security provision ranges from user identification to authentication for physical and logical access control to protected resources.
This white paper was developed by the Smart Card Alliance to describe the role of smart card technology in enhancing the security of FIDO implementations. The white paper includes the following content: An overview of the FIDO principles and protocols A description of the security benefits of using smart card technology in FIDO protocol Tokens This paper describes two novel types of smart card with unconventional form factors, designed to take advantage of common interfaces built into many current handheld devices. Keywords: Mobile Devices, Authentication, Smart Cards.In addition to information security, smart cards achieve greater physical security of services and equipment, because the card restricts access to all but the authorized user(s). E-mail and PCs are being locked-down with smart cards.
This chapter provides a synopsis of the essential principles, methods and strategies for producing secure smart cards and secure smart card applications. The primary problem faced by all information technology systems subject to attack is the avalanche effect that often occurs after a successful attack. Classification of forms of attacks on .Revised and updated edition with new content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking cards, identity cards or passports, and mobile systems security

passive rfid readers schools asset tracking
rf id scanner
Top-up Card before leaving Singapore. Applicable hi! Top-up Cards are $10 hi! Top-up Card, .
smart card security pdf|Smart Card Security and Applications, Second Edition