proxmark3 crack mifare card The first step in cracking a hardened MIFARE card is to discover a valid key. . Get the best deals for nano nfc sim card at eBay.com. We have a great online selection at the lowest prices with Fast & Free shipping on many items!
0 · proxmark3 mifare classic 1k weak / hard
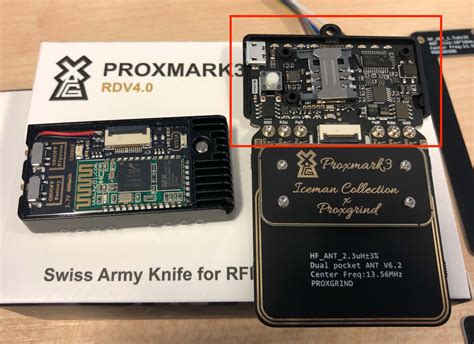
1 · Proxmark3 RDV4
2 · Proxmark3 Mifare Classic 1k (Crack/Dump/Duplicate)
3 · Proxmark3
4 · Proxmark Basics: Cloning MIFARE
5 · Mifare Classic Card cloning with Proxmark3
6 · How to clone MiFare Classic with the Proxmark 3 Easy
7 · Cloning a Mifare Classic 1k card using the Proxmark 3
8 · Breaking Hardened MIFARE with Proxmark3
Before deploying to production, ensure the card readers are thoroughly tested to .

The cloning process. You should now have a proxmark command prompt, so .Proxmark3 Mifare Classic 1k (Crack/Dump/Duplicate) The darkside attack (for weak mifare) . In this post I will share how to clone a MiFare Classic card using the Proxmark 3 . The first step in cracking a hardened MIFARE card is to discover a valid key. .
Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone . Quick summary of operations to crack/dump/duplicate a Mifare classic 1k with . It is an RFID tool that has been used to crack hotel rooms cards and bypass . In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic .
The Proxmark3 is used to show how to clone a Mifare Classic card and the NFC/RFID security . The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the.
proxmark3 mifare classic 1k weak / hard
The cloning process. You should now have a proxmark command prompt, so with a card on the proxmark, assuming it’s a high frequency card, you can: proxmark3> hf search. Which results in a response along the lines of:Proxmark3 Mifare Classic 1k (Crack/Dump/Duplicate) The darkside attack (for weak mifare) can be processed with a low cost hardware like the ARC122U, with mfcuk/mfoc over the libnfc. Nowadays, this attack is not covering a lot of Mifare classic card anymore. The Proxmark is . In this post I will share how to clone a MiFare Classic card using the Proxmark 3 Easy. Requirements: Hardware . Proxmark3 Easy ; Software. The RRG / Iceman git repo (found here: https://github.com/RfidResearchGroup/proxmark3) Process: Obtain keys. Default keys ; Non-default keys; Dump card content; Write dump to empty card; Obtains keys The first step in cracking a hardened MIFARE card is to discover a valid key. This is usually very easy as most cards will have sectors using the default key of FFFFFFFFFFFF. To check a few common keys, try the hf mf chk *1 ? t command: proxmark3> hf mf chk *1 ? t. No key specified, trying default keys .
Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one. Quick summary of operations to crack/dump/duplicate a Mifare classic 1k with the proxmark3. The darkside attack (for weak mifare) can be processed with a low cost hardware like the ARC122U, with mfcuk/mfoc over the libnfc. Nowadays, this attack is not covering a lot of Mifare classic card anymore.
It is an RFID tool that has been used to crack hotel rooms cards and bypass their security systems. The proxmark3 is a powerful general-purpose RFID tool, the size of a deck of cards,.In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic 1K cards using the Proxmark3 RDV4 and the RFID Tools Android App by RRG. Thi.The Proxmark3 is used to show how to clone a Mifare Classic card and the NFC/RFID security of smart cards is discussed.
The first attack on Mifare cards is called Darkside attack, which exploit the weak pseudo-random generator on the card to discover a single key. This attack aims to recover one key from the. The cloning process. You should now have a proxmark command prompt, so with a card on the proxmark, assuming it’s a high frequency card, you can: proxmark3> hf search. Which results in a response along the lines of:Proxmark3 Mifare Classic 1k (Crack/Dump/Duplicate) The darkside attack (for weak mifare) can be processed with a low cost hardware like the ARC122U, with mfcuk/mfoc over the libnfc. Nowadays, this attack is not covering a lot of Mifare classic card anymore. The Proxmark is .
In this post I will share how to clone a MiFare Classic card using the Proxmark 3 Easy. Requirements: Hardware . Proxmark3 Easy ; Software. The RRG / Iceman git repo (found here: https://github.com/RfidResearchGroup/proxmark3) Process: Obtain keys. Default keys ; Non-default keys; Dump card content; Write dump to empty card; Obtains keys The first step in cracking a hardened MIFARE card is to discover a valid key. This is usually very easy as most cards will have sectors using the default key of FFFFFFFFFFFF. To check a few common keys, try the hf mf chk *1 ? t command: proxmark3> hf mf chk *1 ? t. No key specified, trying default keys .
Proxmark3 RDV4
Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one.
Quick summary of operations to crack/dump/duplicate a Mifare classic 1k with the proxmark3. The darkside attack (for weak mifare) can be processed with a low cost hardware like the ARC122U, with mfcuk/mfoc over the libnfc. Nowadays, this attack is not covering a lot of Mifare classic card anymore.
It is an RFID tool that has been used to crack hotel rooms cards and bypass their security systems. The proxmark3 is a powerful general-purpose RFID tool, the size of a deck of cards,.In this Tradecraft tutorial, we will be decyphering and emulating Mifare Classic 1K cards using the Proxmark3 RDV4 and the RFID Tools Android App by RRG. Thi.
Proxmark3 Mifare Classic 1k (Crack/Dump/Duplicate)
Proxmark3
Use a Mobile Scan. Some modern smartphones can scan NFC cards using their built-in NFC .
proxmark3 crack mifare card|How to clone MiFare Classic with the Proxmark 3 Easy