secure symmetric authentication for rfid tags pdf In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is . About logos. 2018 NFL Playoff Standings. Previous Season Next Season. Super Bowl Champion: New England Patriots. AP MVP: Patrick Mahomes. AP Offensive Rookie of the Year: Saquon .
0 · rfid authentication protocol
1 · rfid authentication algorithm
2 · aes rfid
NFC Inkjet PVC Cards (NTAG215) – Waterproof, Double-Sided Print, Compatible .How to Customize and Use Your NFC PVC Card: A Step-by-Step Guide Step 1: Choose Your Card Design and Finish Your journey to creating a customized NFC PVC card begins with selecting the card that best suits your style and needs. Start by choosing the card .
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is .
Request PDF | Secure symmetric authentication for RFID tags | The project ART proposes to enhance passive RFID (Radio Frequency Identification) tags with .
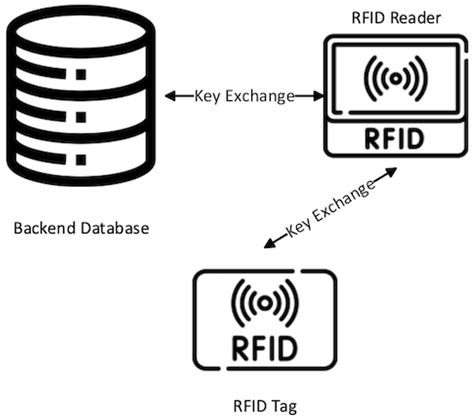
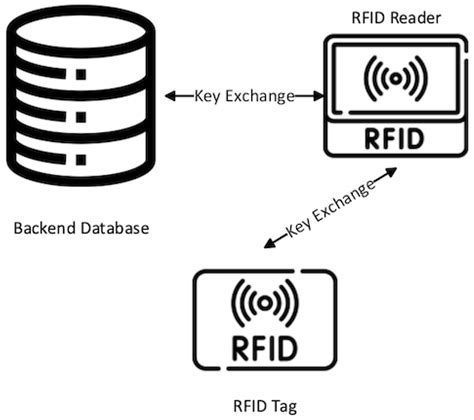
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Request PDF | Secure symmetric authentication for RFID tags | The project ART proposes to enhance passive RFID (Radio Frequency Identification) tags with cryptographically secure.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.
rfid authentication protocol
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
When a tagged object is placed in the magnetic field of a reader, the information is exchanged between the tag and the reader based on a specific com-munication protocol, and the tag can send its unique identifier to the reader in a wireless manner.In this paper, we proposed a secure ECC-based RFID authentication scheme to achieve mutual authentication using both secure ID-verifier transfer and challenge-response protocols. Moreover, the proposed scheme can satisfy the security requirements of RFID.
Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project
rfid authentication algorithm
SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Request PDF | Secure symmetric authentication for RFID tags | The project ART proposes to enhance passive RFID (Radio Frequency Identification) tags with cryptographically secure.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.
aes rfid
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.When a tagged object is placed in the magnetic field of a reader, the information is exchanged between the tag and the reader based on a specific com-munication protocol, and the tag can send its unique identifier to the reader in a wireless manner.
In this paper, we proposed a secure ECC-based RFID authentication scheme to achieve mutual authentication using both secure ID-verifier transfer and challenge-response protocols. Moreover, the proposed scheme can satisfy the security requirements of RFID. Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al.
Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project
View scores and results from week 1 of the 2019 NFL Postseason
secure symmetric authentication for rfid tags pdf|rfid authentication protocol